Iran Linked Hackers Hit Israeli Sectors With New MuddyViper Backdoor
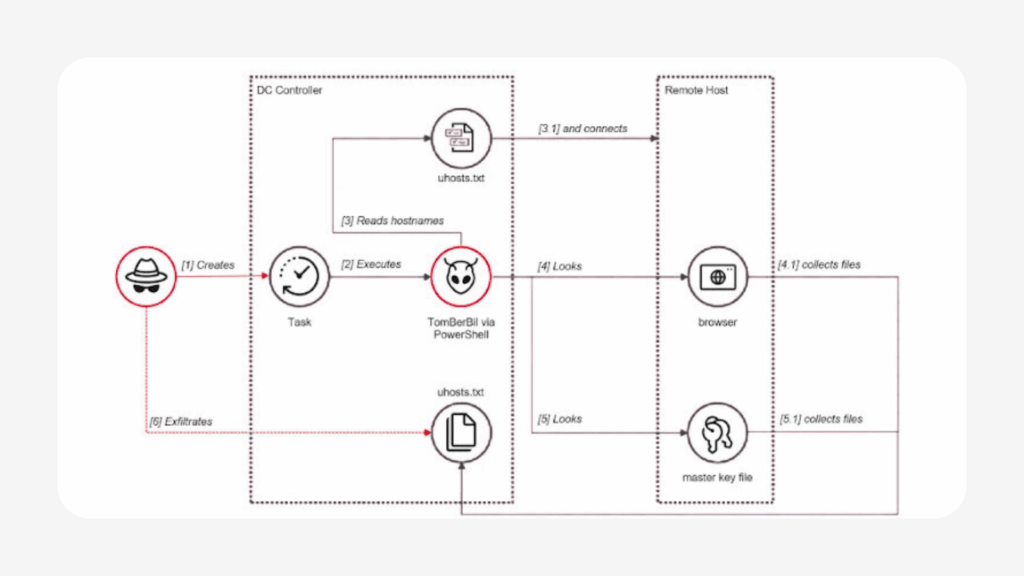
Israeli organizations across academia, engineering, local government, manufacturing, technology, transportation, and utilities have become targets of a sophisticated campaign by Iranian-linked hackers deploying a new backdoor called MuddyViper. ESET attributed the attacks to the MuddyWater group, also known as Mango Sandstorm or TA450, linked to Iran’s Ministry of Intelligence and Security (MOIS). One Egyptian technology […]
Iran Linked Hackers Hit Israeli Sectors With New MuddyViper Backdoor Read More »