Fake Chrome Extension Safery Steals Ethereum Wallet Seed Phrases via Sui Blockchain
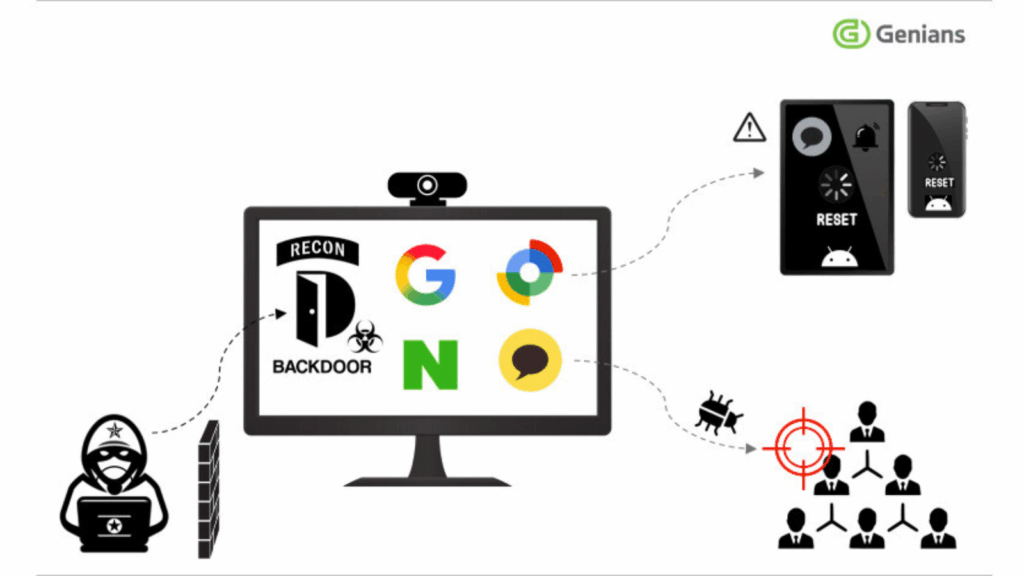
bersecurity researchers have discovered a malicious Chrome extension masquerading as a legitimate Ethereum wallet that secretly steals users’ seed phrases through an advanced blockchain-based exfiltration technique. The extension, named “Safery: Ethereum Wallet,” was falsely promoted as a secure Ethereum wallet for managing cryptocurrency with customizable settings. It was first uploaded to the Chrome Web Store […]
Fake Chrome Extension Safery Steals Ethereum Wallet Seed Phrases via Sui Blockchain Read More »