Vibe-Coded Malicious VS Code Extension Found Containing Built-In Ransomware Functionality
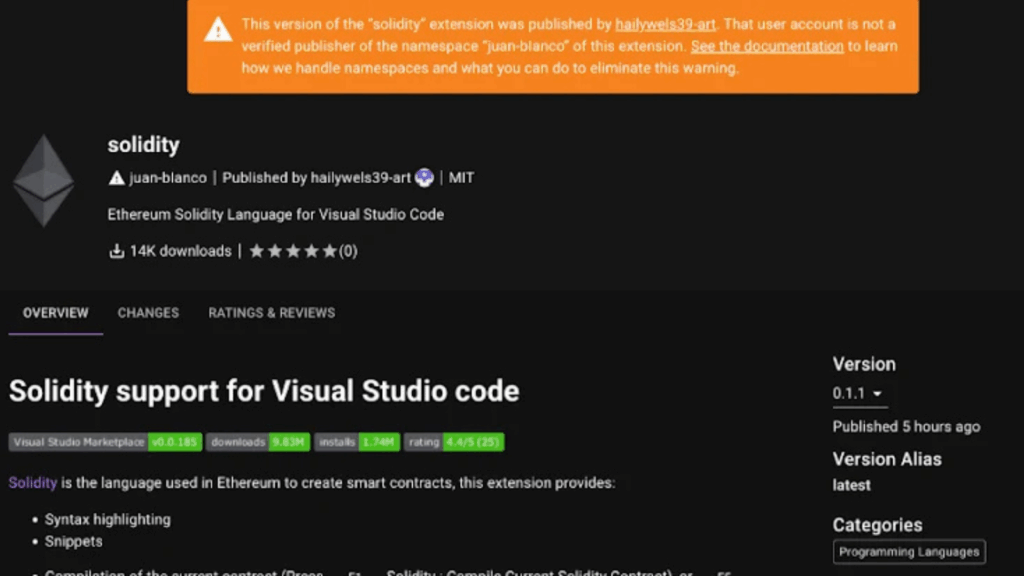
Cybersecurity researchers have uncovered a malicious extension for Microsoft’s Visual Studio Code (VS Code) that contains basic ransomware functionality. The extension, which appears to have been “vibe-coded” or created with the assistance of artificial intelligence, highlights a new frontier in software supply chain threats. A Brazenly Malicious Extension Discovered by Secure Annex researcher John Tuckner, […]