North Korean Hackers Merge BeaverTail and OtterCookie into Sophisticated JavaScript Malware
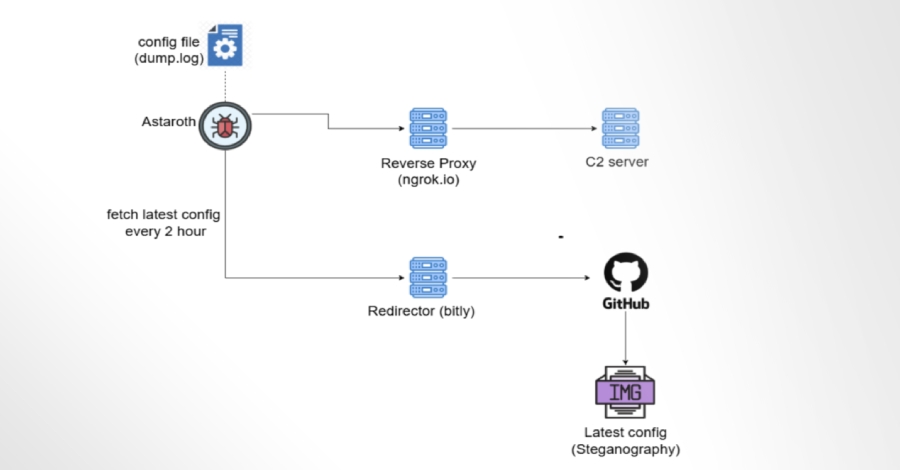
North Korean hackers linked to the Contagious Interview campaign are enhancing their malicious tools by merging two major malware families, BeaverTail and OtterCookie. This evolution, observed by Cisco Talos, shows that the group is actively upgrading its capabilities and refining its JavaScript-based attack methods. Ongoing Campaign and New Findings According to Cisco Talos, the recent […]