New FileFix variant spreads StealC malware via multilingual phishing site
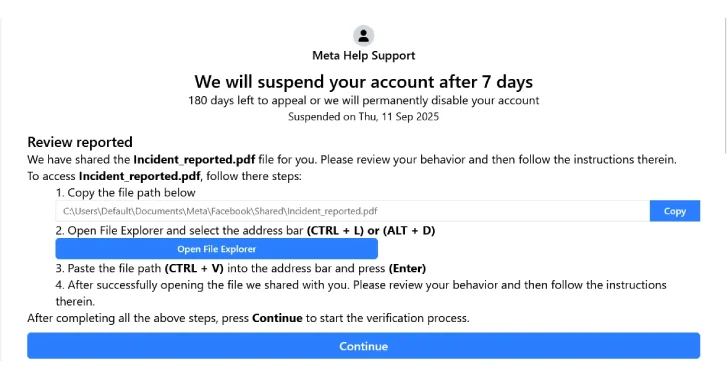
Cybersecurity researchers are tracking a fresh campaign that uses a new FileFix variant to deliver the StealC information stealer malware. The attack relies on a convincing, multilingual phishing site, advanced obfuscation, and anti-analysis tricks to avoid detection, according to an Acronis researcher, Eliad Kimhy, in a report shared with The Hacker News. How the attack […]
New FileFix variant spreads StealC malware via multilingual phishing site Read More »