Indian Users Targeted in Tax Phishing Campaign Delivering Blackmoon Malware
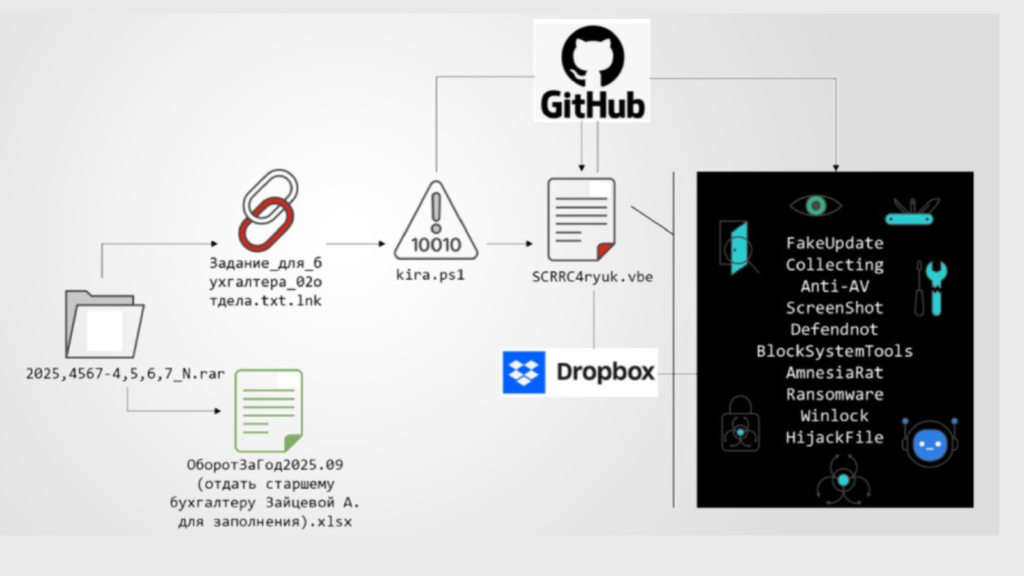
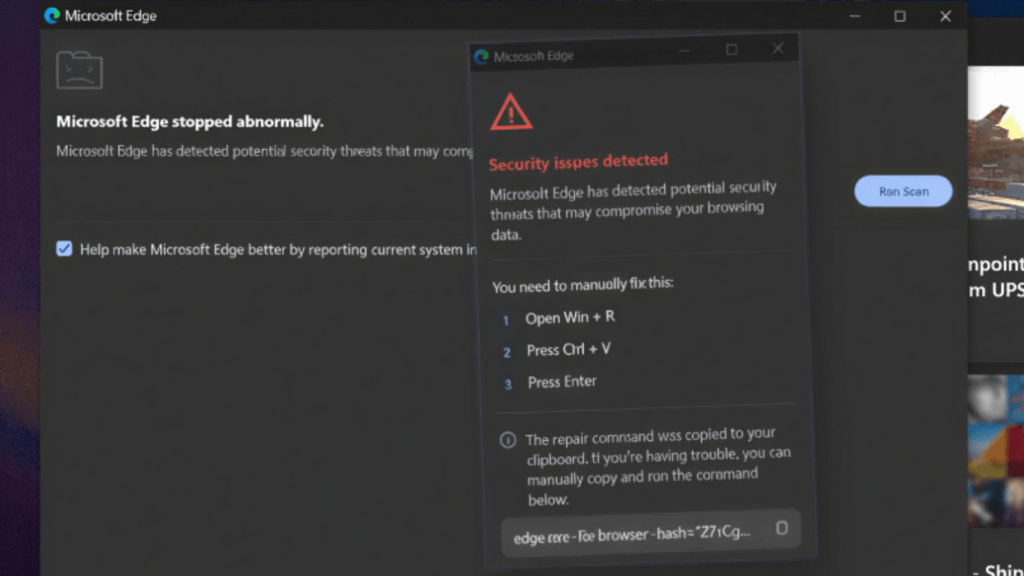
Cybersecurity researchers have identified an active phishing campaign targeting users in India as part of a suspected cyber espionage operation. The campaign delivers a multi-stage backdoor designed to provide long-term access, continuous surveillance, and data exfiltration from infected systems. According to the eSentire Threat Response Unit (TRU), the attackers are distributing phishing emails that impersonate […]
Indian Users Targeted in Tax Phishing Campaign Delivering Blackmoon Malware Read More »