Hackers Abuse c-ares DLL Side-Loading to Evade Security and Deploy Malware
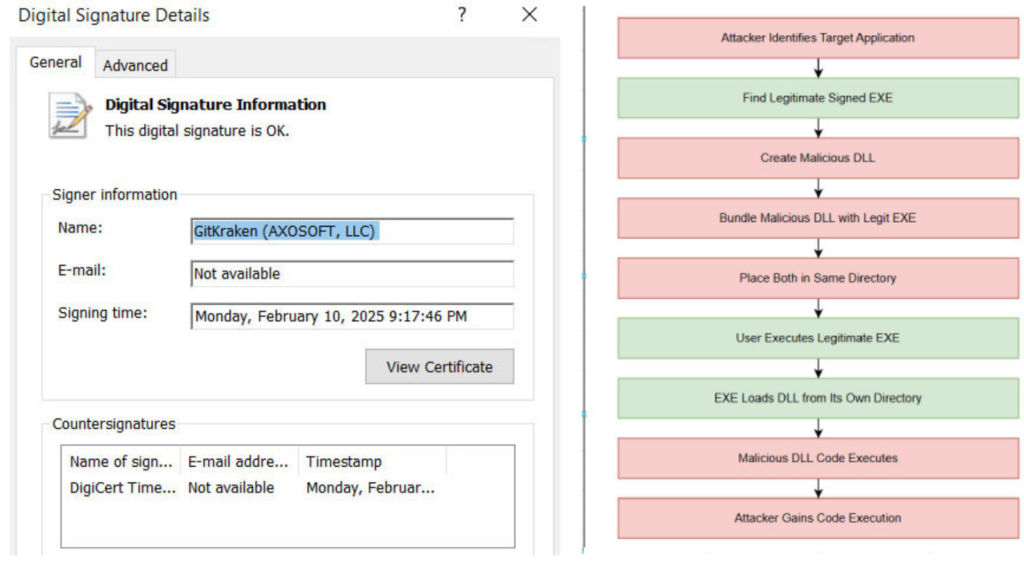
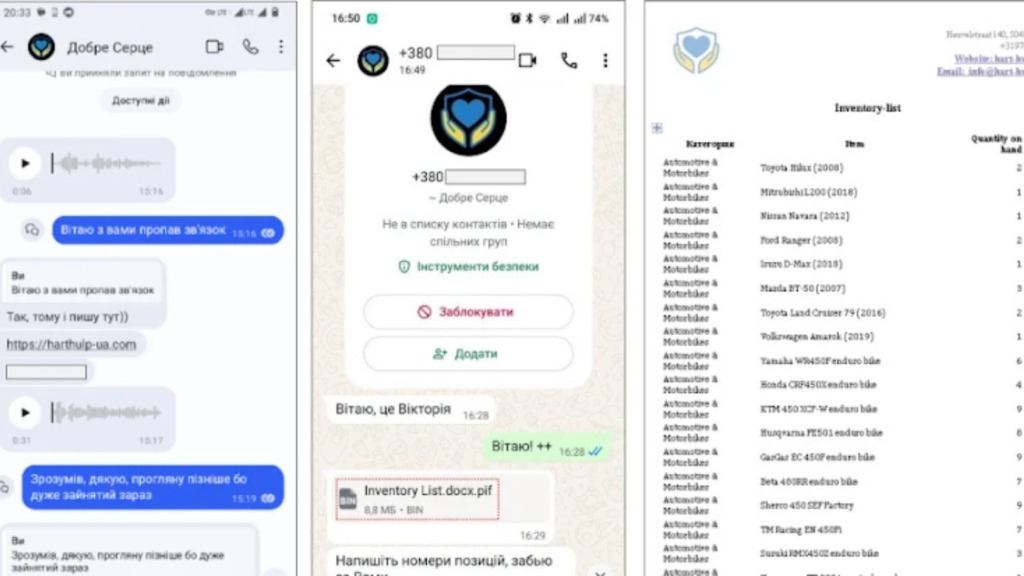
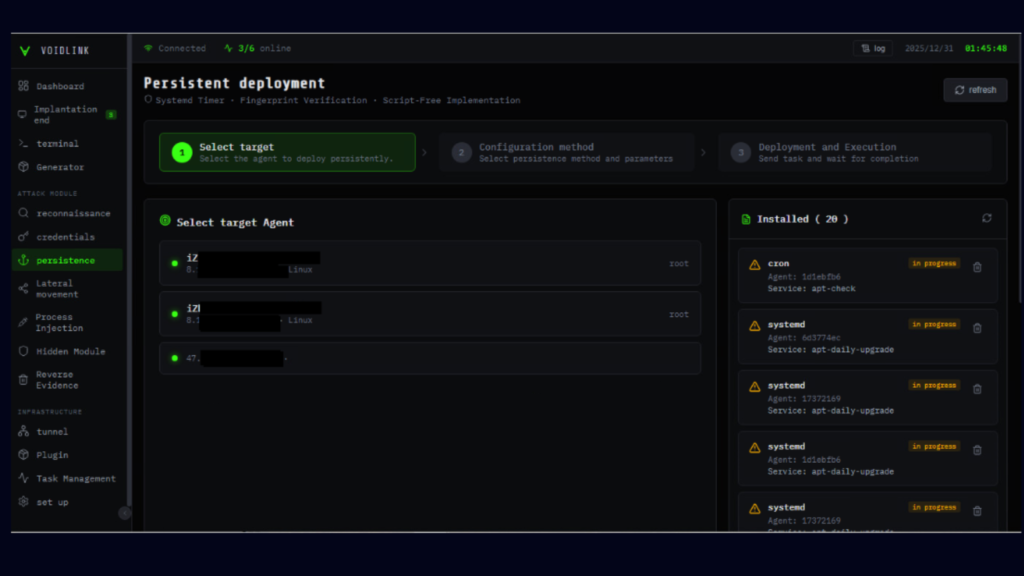
Cybersecurity researchers have uncovered an active malware campaign that abuses a DLL side-loading weakness in a legitimate binary linked to the open-source c-ares library. By exploiting this technique, attackers are able to bypass traditional security controls and deliver a wide range of commodity malware, including trojans, stealers, and remote access tools. How the Attack Works According to […]
Hackers Abuse c-ares DLL Side-Loading to Evade Security and Deploy Malware Read More »