Rust Based VENON Malware Targets 33 Brazilian Banks with Credential Stealing Overlays
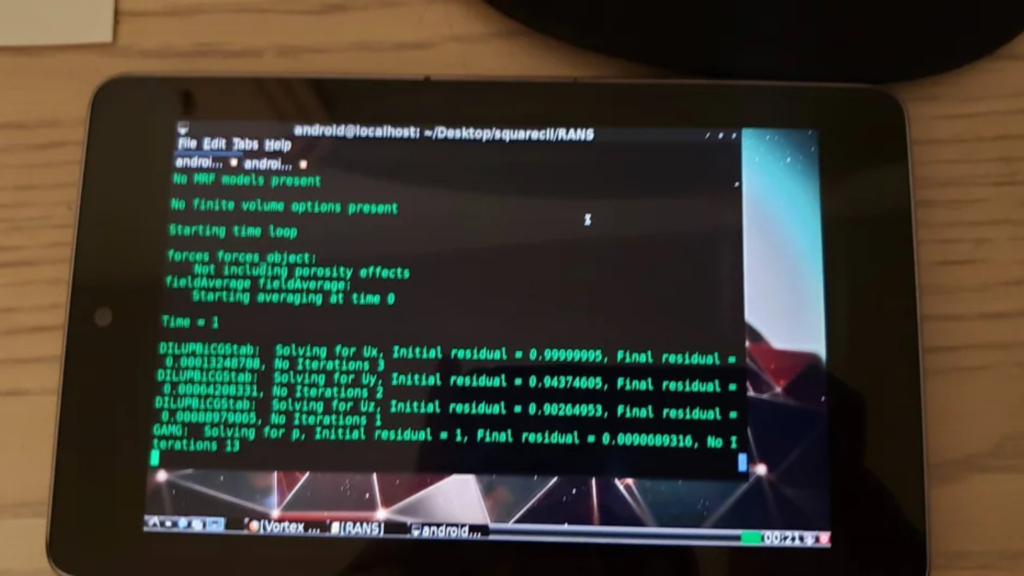
Cybersecurity researchers have uncovered a newly developed banking malware named VENON, which specifically targets users in Brazil. The malware is written in Rust, marking a notable shift from the traditional Delphi-based malware families commonly associated with the Latin American cybercrime landscape. The malicious program, designed to infect Windows systems, was discovered recently and analyzed by the Brazilian cybersecurity firm ZenoX. […]
Rust Based VENON Malware Targets 33 Brazilian Banks with Credential Stealing Overlays Read More »