Researchers Bypass Perplexity Comet AI Browser Safeguards to Launch Phishing Scam in Minutes
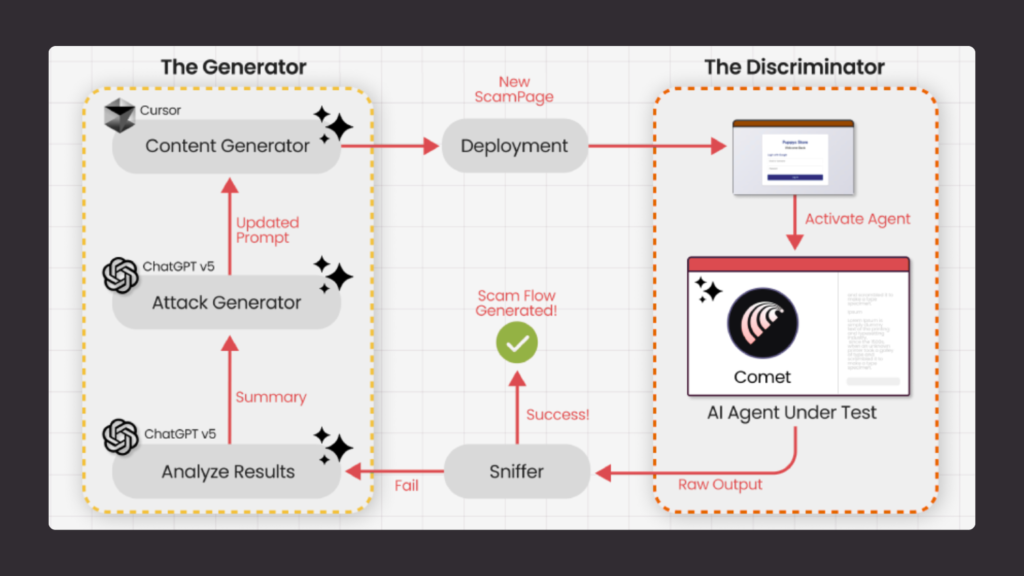
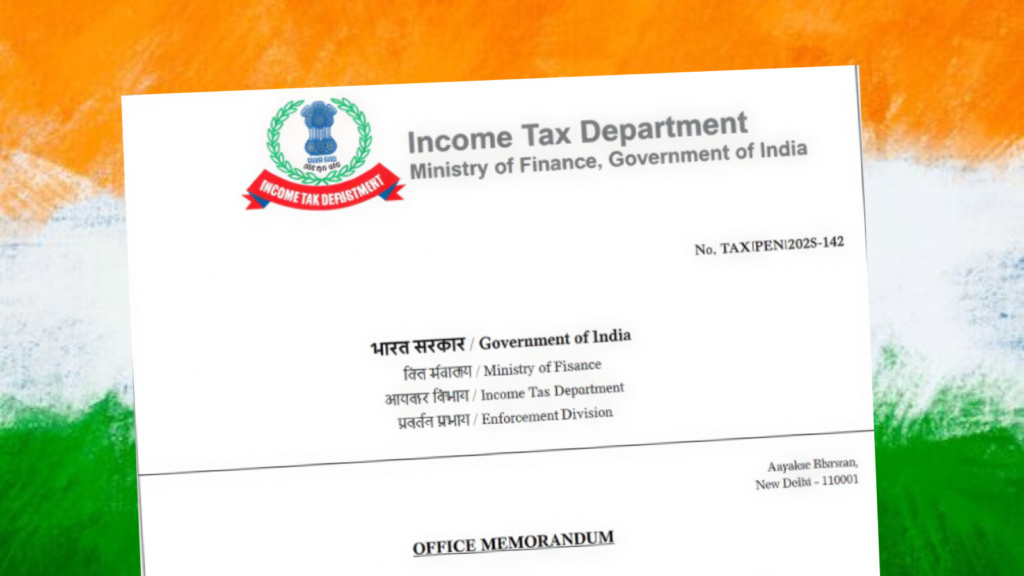
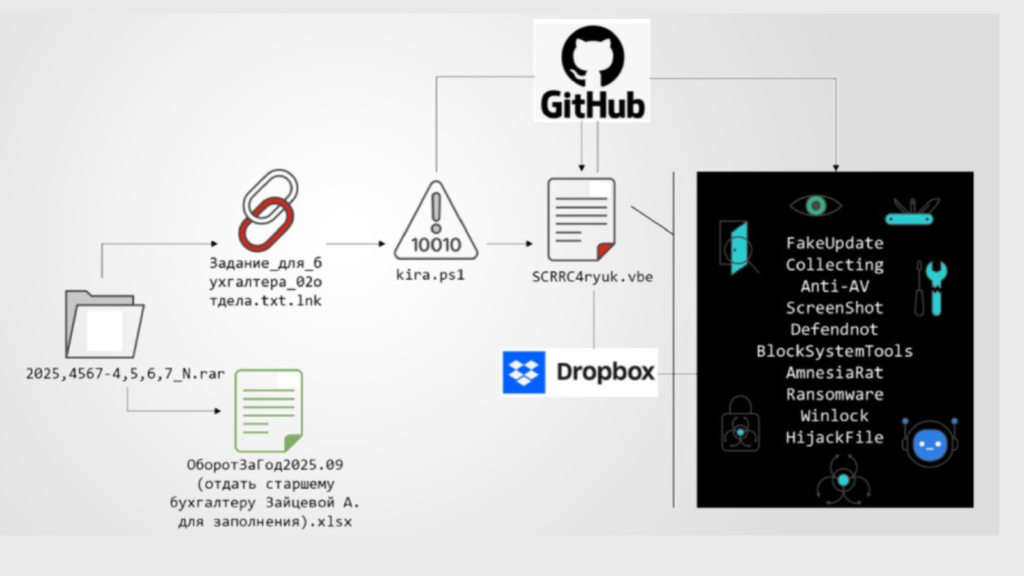
Cybersecurity researchers have demonstrated how an artificial intelligence powered web browser can be manipulated into executing a phishing scam in just a few minutes. The attack targeted the Comet AI browser developed by Perplexity, highlighting emerging risks in agentic AI browsing technologies. Agentic browsers use artificial intelligence to automatically interact with websites, complete tasks, and make […]