Microsoft Flags Multi-Stage AitM Phishing and BEC Attacks Targeting Energy Firms
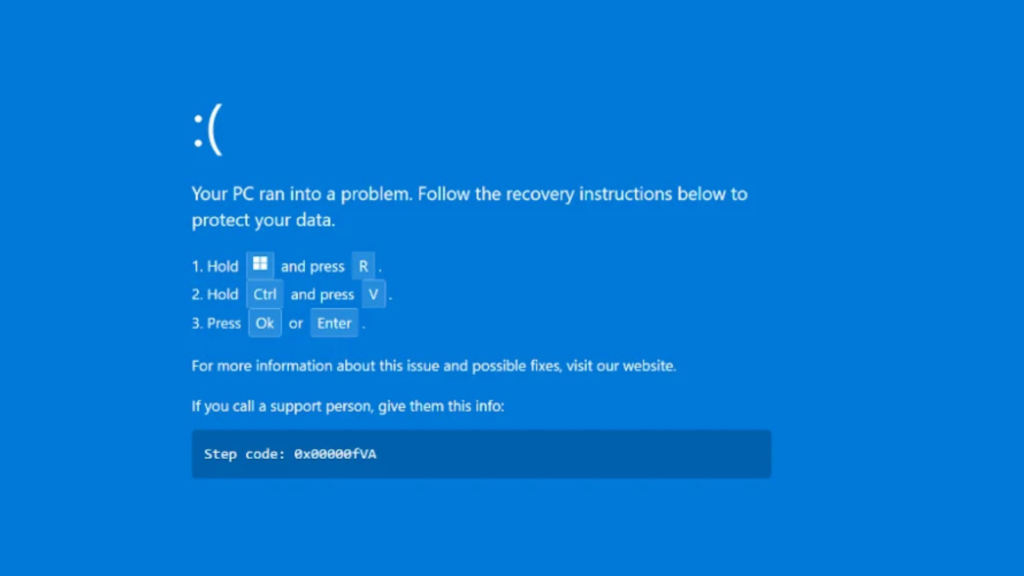
Microsoft has issued an alert regarding a sophisticated multi-stage adversary-in-the-middle (AitM) phishing campaign combined with business email compromise (BEC) activity, primarily targeting organizations operating in the energy sector. According to the Microsoft Defender Security Research Team, the attackers exploited SharePoint file-sharing services to distribute phishing content while creating inbox rules to remain persistent and avoid […]
Microsoft Flags Multi-Stage AitM Phishing and BEC Attacks Targeting Energy Firms Read More »