Ukraine Aid Organizations Targeted via Fake Zoom Meetings and Malicious PDF Files
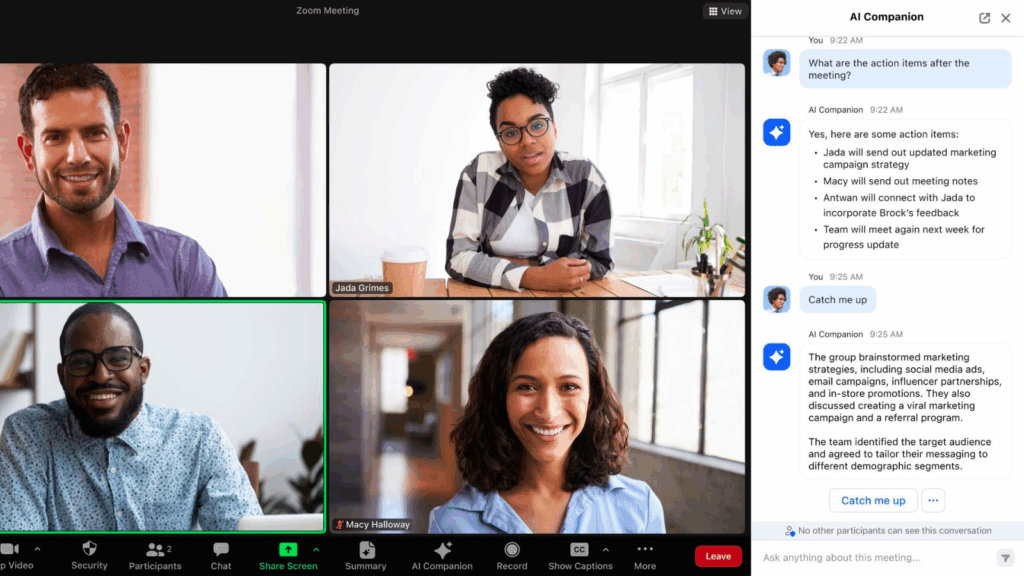
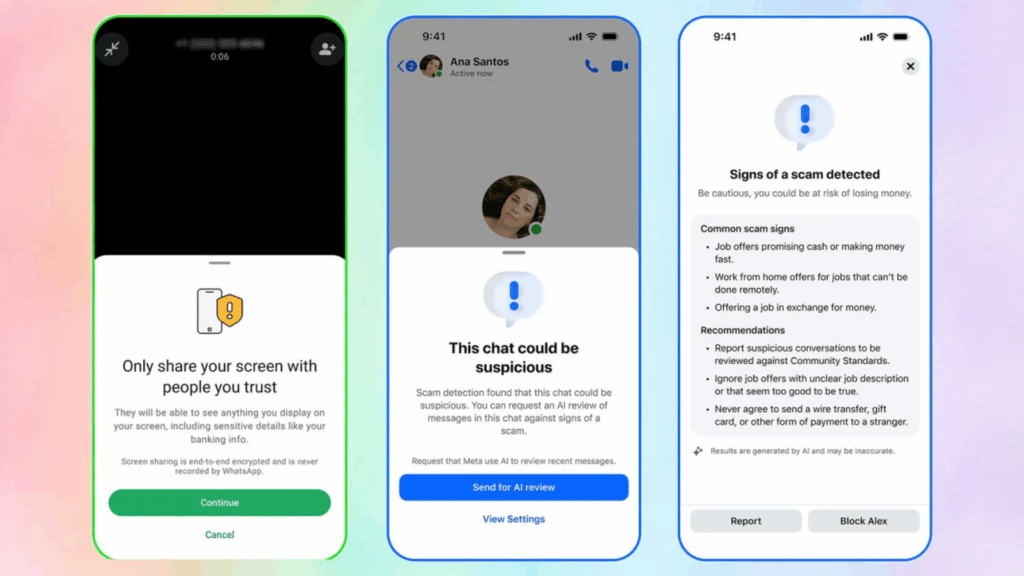
A recent spear-phishing operation, named PhantomCaptcha, has targeted organizations involved in Ukraine’s humanitarian and war relief efforts. Cybersecurity researchers reported that the campaign delivers a remote access trojan (RAT) using WebSocket connections for command-and-control (C2), posing a serious threat to international relief organizations. Scope of the Attack On October 8, 2025, individual members of the […]
Ukraine Aid Organizations Targeted via Fake Zoom Meetings and Malicious PDF Files Read More »