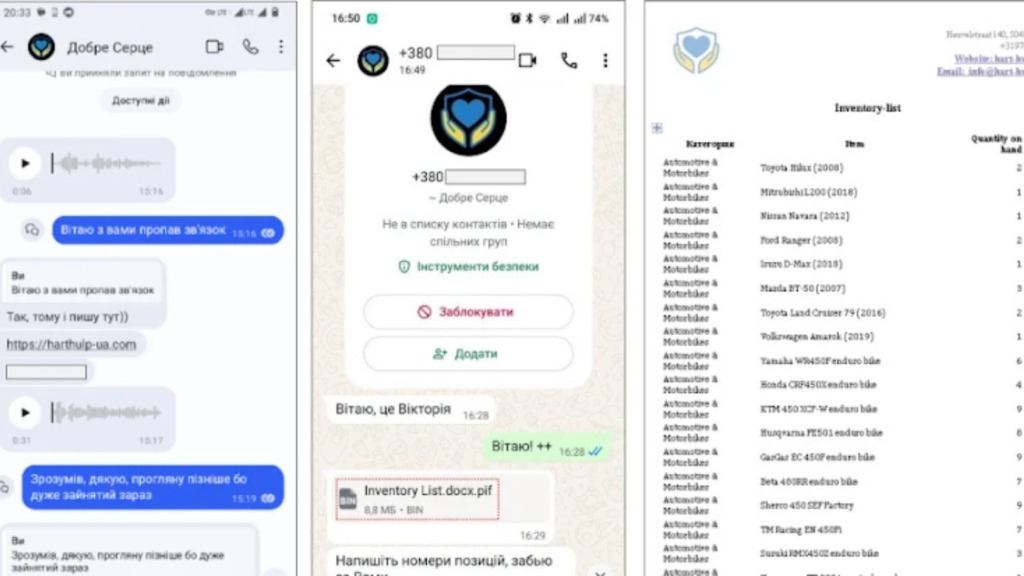
PLUGGYAPE Malware Uses Signal and WhatsApp to Target Ukrainian Defense Forces
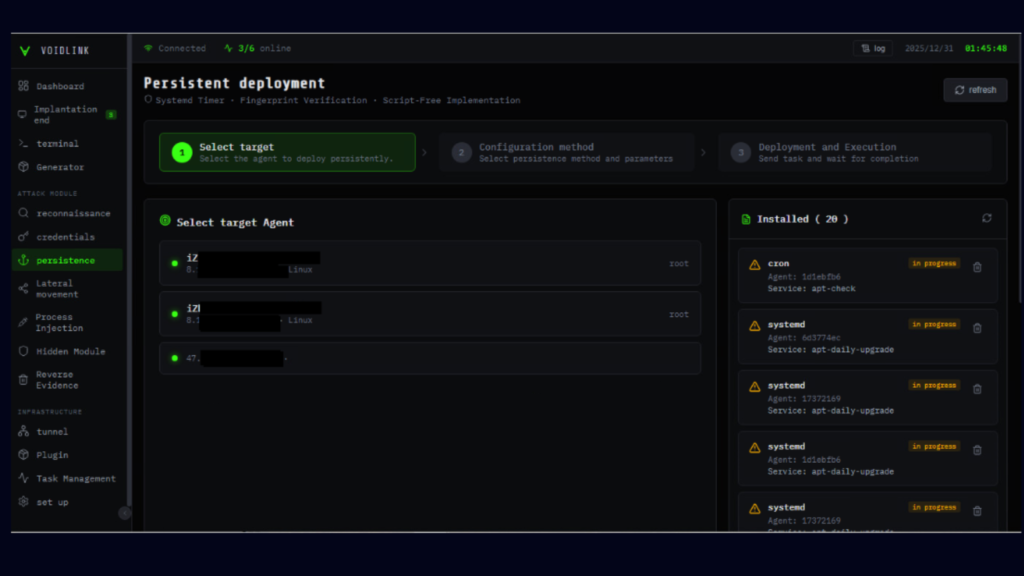
Ukraine’s Computer Emergency Response Team (CERT-UA) has revealed details of a recent cyber espionage campaign targeting Ukrainian defense forces using a malware strain known as PLUGGYAPE. The attacks were observed between October and December 2025. CERT-UA has attributed the activity with medium confidence to a Russia aligned threat group tracked as Void Blizzard, also known […]
PLUGGYAPE Malware Uses Signal and WhatsApp to Target Ukrainian Defense Forces Read More »