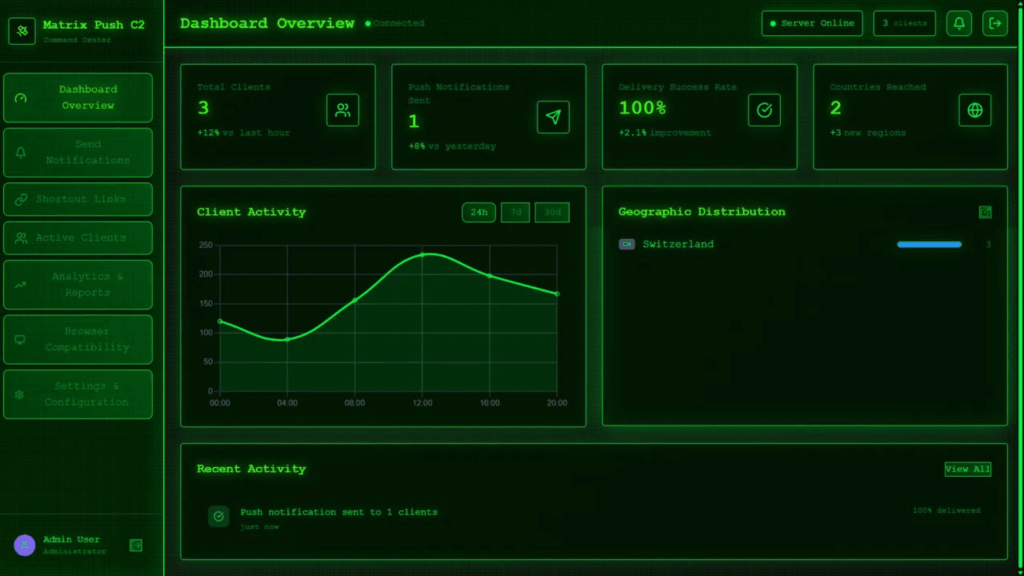
Silver Fox Distributes ValleyRAT in China Through Fake Microsoft Teams Installer
A new campaign linked to the threat actor Silver Fox is targeting Chinese speaking users through a deceptive installer that pretends to be Microsoft Teams. The operation appears to be a false flag attempt designed to resemble activity from a Russian group, although the final payload is ValleyRAT, a malware family associated with Chinese cybercrime […]
Silver Fox Distributes ValleyRAT in China Through Fake Microsoft Teams Installer Read More »