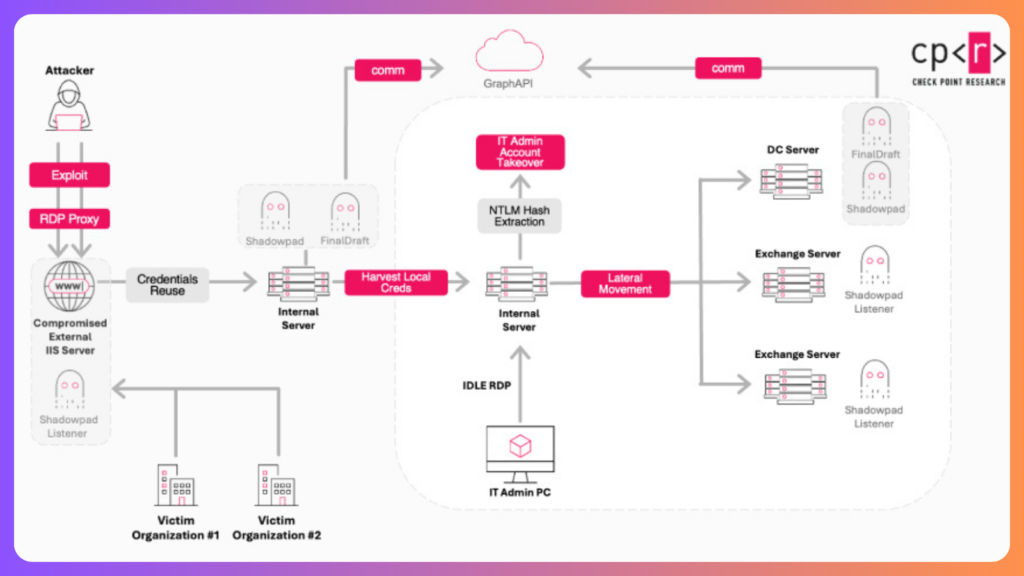
China Aligned Threat Group Abuses Windows Group Policy to Deploy Espionage Malware
A previously undocumented China-aligned threat cluster, tracked as LongNosedGoblin, has been linked to a series of cyber espionage operations targeting government organizations in Southeast Asia and Japan. The activity, uncovered by Slovak cybersecurity firm ESET, has been assessed to be active since at least September 2023, with intelligence collection identified as the primary objective. According […]
China Aligned Threat Group Abuses Windows Group Policy to Deploy Espionage Malware Read More »