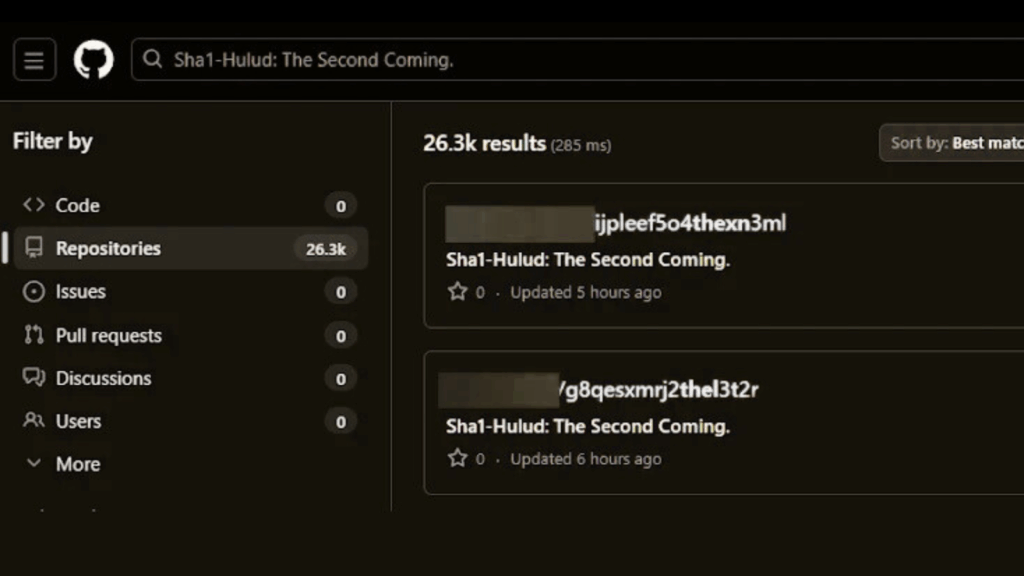
Years of leaks from JSONFormatter and CodeBeautify have exposed thousands of passwords and API keys, creating major security risks
A new investigation has uncovered that sensitive credentials from governments, telecoms, financial institutions, and critical infrastructure have been unintentionally exposed through popular online code formatting tools such as JSONFormatter and CodeBeautify. These websites, commonly used to validate or beautify JSON and other code snippets, have become unintended repositories of private information due to users pasting […]