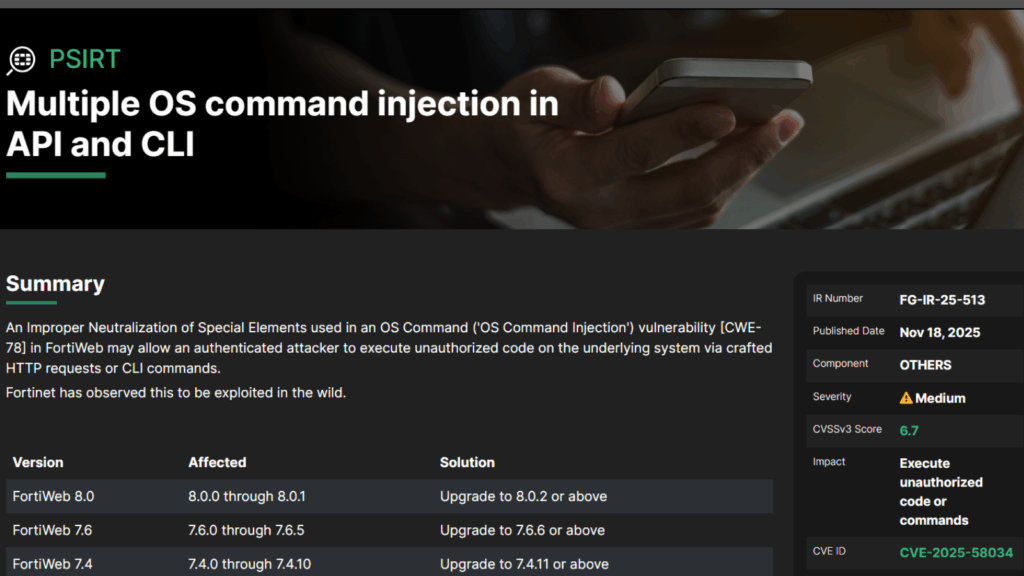
Fortinet Alerts Users About FortiWeb CVE 2025 58034 Vulnerability Now Being Actively Exploited
Fortinet has issued an important warning regarding a newly discovered security flaw in its FortiWeb product. The vulnerability, identified as CVE 2025 58034, has already been exploited in real world attacks, raising concerns for organizations that rely on FortiWeb for application security. About the Vulnerability This flaw is rated as medium severity and has a […]