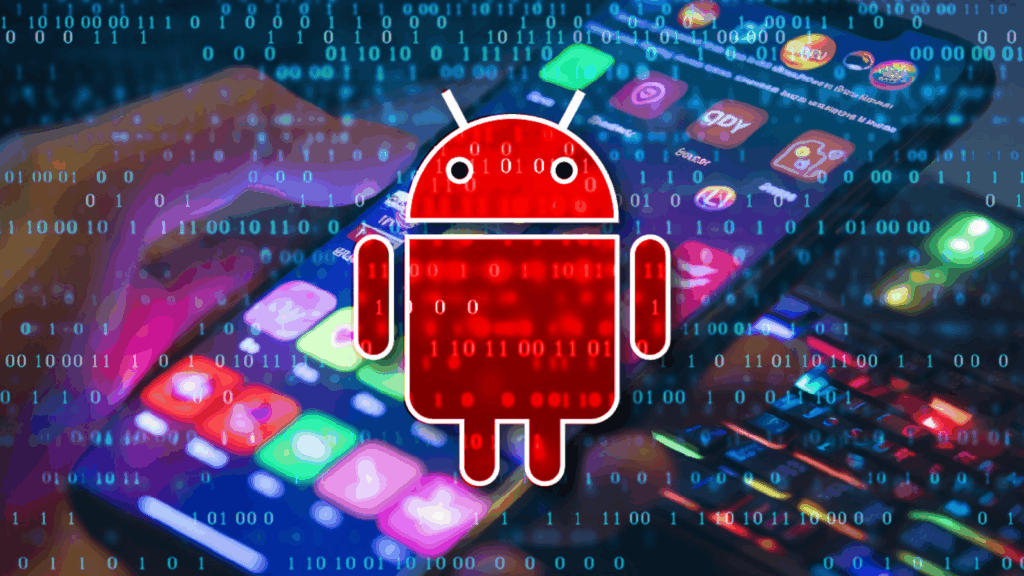
Trojanized Gaming Tools Distribute Java Based RAT Through Browsers and Chat Platforms
Cybersecurity researchers are warning that attackers are disguising malicious software as popular gaming utilities to infect unsuspecting users. The campaign relies on browser downloads and chat platform sharing to deliver a Java based remote access trojan, enabling full control over compromised systems. According to the Microsoft Threat Intelligence team, the infection process begins with a malicious downloader […]
Trojanized Gaming Tools Distribute Java Based RAT Through Browsers and Chat Platforms Read More »