New Android Trojan ‘Herodotus’ Evades Anti-Fraud Systems by Mimicking Human Typing Behavior
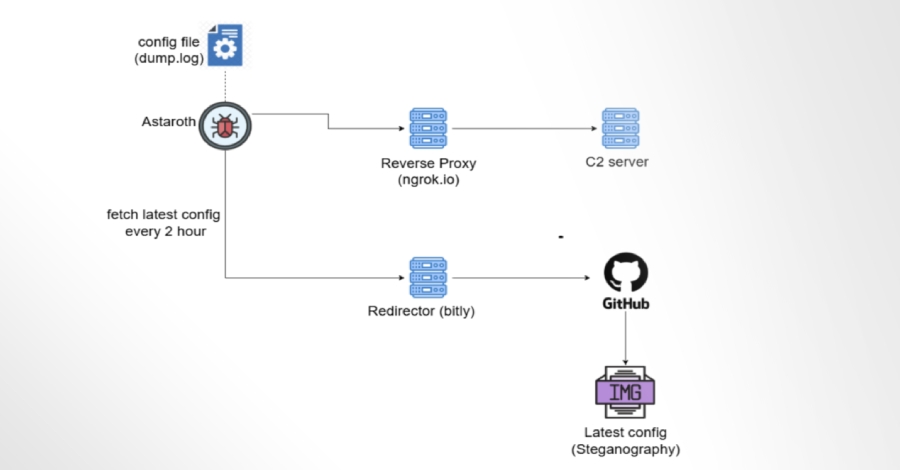
Security researchers have uncovered a new Android banking trojan, named Herodotus, which is being used in active campaigns targeting users in Italy and Brazil. The malware aims for device takeover, or DTO, and stands out because it deliberately mimics human typing patterns to evade timing-based, behaviour-only anti-fraud systems. What Herodotus is, and where it came […]