Amazon Uncovers Cyberattacks Exploiting Cisco ISE and Citrix NetScaler Zero-Day Vulnerabilities
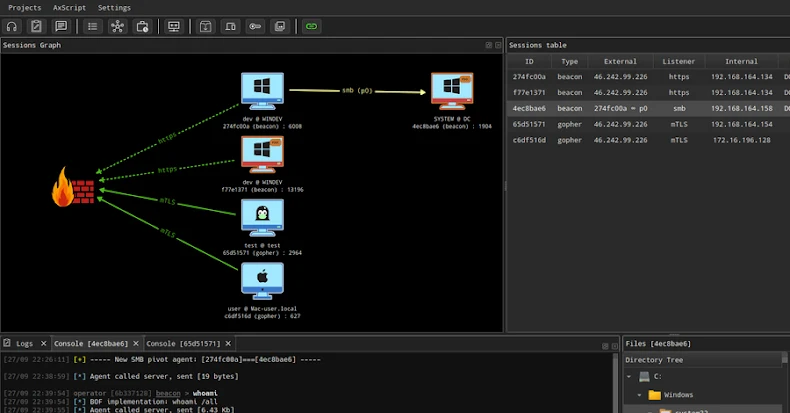
Amazon’s threat intelligence division has discovered an ongoing campaign that exploits two critical zero-day vulnerabilities in Cisco Identity Services Engine (ISE) and Citrix NetScaler ADC systems. These flaws are being weaponized by a highly advanced threat actor to deploy custom-built malware aimed at infiltrating enterprise environments. Critical Vulnerabilities Under Attack The attack campaign takes advantage […]