Critical Tableau Server Flaw Allows Attackers to Upload and Execute Malicious Files
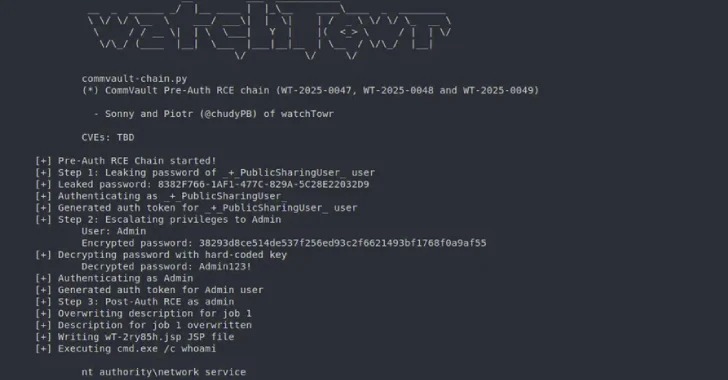
A severe security flaw has been discovered in Tableau Server, which could allow attackers to upload and execute malicious files, leading to full system takeover. This vulnerability, tracked as CVE-2025-26496 with a CVSS score of 9.6, impacts several versions of Tableau Server and Tableau Desktop on both Windows and Linux platforms. Key Highlights Tableau Server […]
Critical Tableau Server Flaw Allows Attackers to Upload and Execute Malicious Files Read More »