Cybersecurity researchers have uncovered a sophisticated adversary-in-the-middle framework named DKnife, which has been operated by China-linked threat actors since at least 2019. The framework is designed to compromise routers and edge devices, enabling large-scale traffic interception, credential theft, and targeted malware distribution.
According to a report published by Cisco Talos, DKnife consists of multiple Linux-based implants that perform deep packet inspection, manipulate network traffic, and hijack software updates to deploy malicious payloads. Evidence suggests that the framework primarily targets Chinese-speaking users.
This assessment is based on the presence of phishing pages for Chinese email providers, data exfiltration modules for widely used Chinese mobile applications such as WeChat, and internal code references to Chinese media platforms.
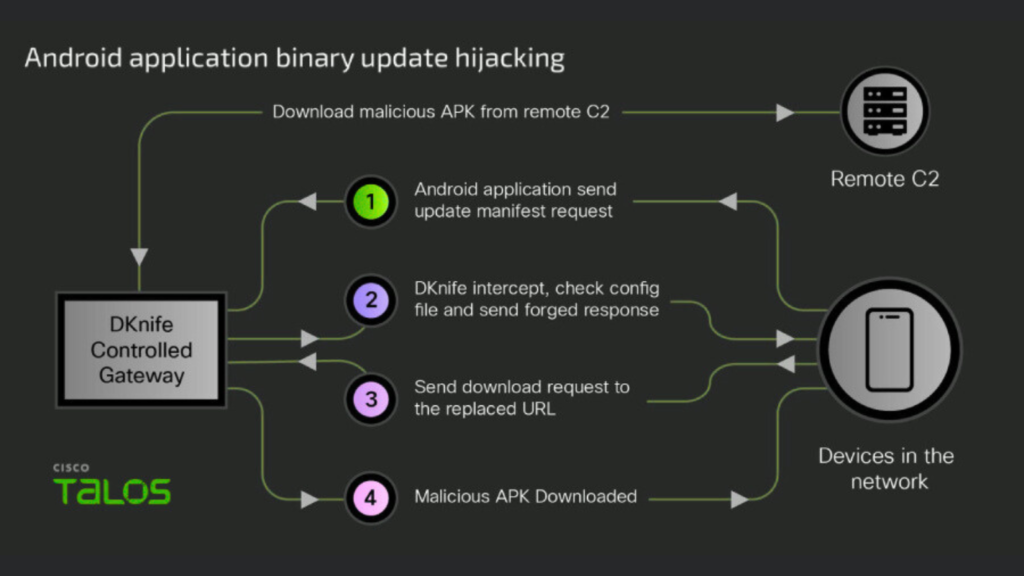
Cisco Talos researcher Ashley Shen stated that DKnife attacks affect a wide spectrum of devices, including desktop systems, mobile phones, and Internet of Things devices. The framework is actively used to deliver and communicate with advanced backdoors such as ShadowPad and DarkNimbus by intercepting legitimate binary downloads and Android application updates.
Relationship With Chinese Threat Ecosystem
Talos identified DKnife while tracking activity linked to another Chinese threat cluster known as Earth Minotaur, which is associated with the MOONSHINE exploit kit and the DarkNimbus backdoor. Notably, DarkNimbus has also been used by a separate China-aligned advanced persistent threat group called TheWizards.
Infrastructure analysis revealed overlaps between DKnife and WizardNet, a Windows-based implant deployed by TheWizards through a separate AitM framework known as Spellbinder. Details of Spellbinder were previously documented by ESET in April 2025.
The targeting of Chinese-speaking users appears to be based on configuration data recovered from a single command-and-control server. Researchers believe additional C2 servers may exist with configurations tailored for other geographic regions.
This finding is significant due to known operational links between DKnife and TheWizards, a group that has targeted individuals and gambling-related entities in Cambodia, Hong Kong, Mainland China, the Philippines, and the United Arab Emirates.
Modular Architecture and Core Components
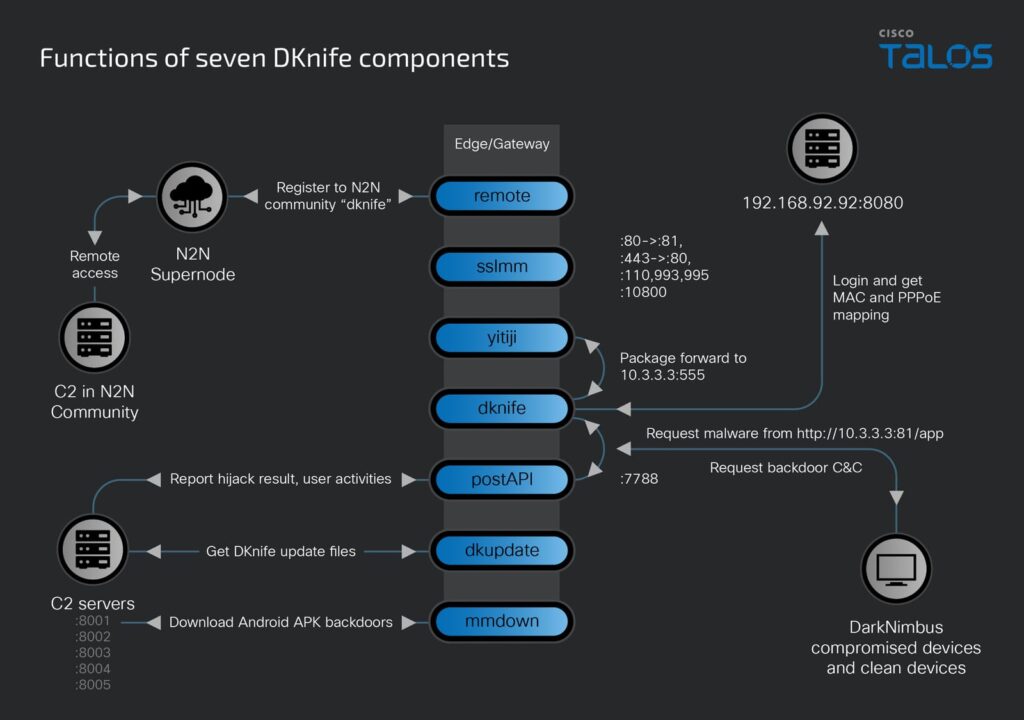
Unlike WizardNet, which targets Windows systems, DKnife is built exclusively for Linux-based routers and edge devices. It uses a modular architecture delivered through an ELF downloader, allowing operators to selectively enable functionality based on campaign objectives.
The framework includes seven primary components:
- dknife.bin
Acts as the core engine, responsible for deep packet inspection, user activity monitoring, DNS hijacking, and binary download manipulation - postapi.bin
Serves as a relay module that receives harvested data from DKnife and forwards it to remote C2 servers - sslmm.bin
A modified reverse proxy derived from HAProxy that performs TLS termination, decrypts email traffic, and reroutes URLs - mmdown.bin
Connects to a hard-coded C2 server to retrieve malicious Android application packages - yitiji.bin
Creates a bridged TAP interface on the router to forward attacker-injected LAN traffic - remote.bin
A peer-to-peer VPN client that establishes persistent communication channels with remote infrastructure - dkupdate.bin
Functions as an updater and watchdog, ensuring all components remain active
Credential Harvesting and Traffic Manipulation
Cisco Talos confirmed that DKnife can steal credentials from a major Chinese email provider and host phishing pages for additional services. The sslmm.bin module presents a rogue TLS certificate to victims, decrypts POP3 and IMAP sessions, and inspects plaintext traffic to extract usernames and passwords.
Stolen credentials are tagged internally and forwarded to the postapi.bin module before being relayed to command-and-control servers.
The primary intelligence collection and attack logic resides in dknife.bin, which allows operators to conduct both passive surveillance and active in-line attacks. These capabilities include:
- Supplying updated C2 addresses to Android and Windows variants of DarkNimbus
- Performing DNS hijacking over IPv4 and IPv6 to redirect traffic related to JD.com domains
- Hijacking Android application updates for Chinese news platforms, video streaming services, image editors, e-commerce apps, taxi services, gaming platforms, and adult video apps
- Replacing Windows and other binary downloads with malicious payloads using DLL side-loading to deploy ShadowPad, which then loads DarkNimbus
- Disrupting communications from antivirus and system management tools such as 360 Total Security and Tencent services
- Monitoring user behavior in real time and categorizing activity across messaging apps, voice and video calls, shopping, news consumption, map searches, video streaming, gaming, dating platforms, ride-hailing services, and email usage
Strategic Implications
Cisco Talos emphasized that routers and edge devices remain highly attractive targets for advanced threat actors due to their visibility into network traffic and lack of monitoring. The discovery of DKnife highlights the growing sophistication of modern AitM frameworks, which combine deep packet inspection, traffic interception, and customized malware delivery across multiple device ecosystems.
As attackers continue to focus on network infrastructure, understanding these tools and their techniques remains critical for defenders worldwide.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.