A China-linked advanced persistent threat group has been linked to a sophisticated cyber espionage campaign that relied on Domain Name System (DNS) poisoning to distribute the MgBot backdoor. The attacks targeted selected victims across Türkiye, China, and India, according to new findings from Kaspersky.
Kaspersky researchers observed the activity between November 2022 and November 2024 and attributed it to the hacking group known as Evasive Panda. The group is also tracked under the names Bronze Highland, Daggerfly, and StormBamboo, and is believed to have been active since at least 2012.
According to Kaspersky researcher Fatih Şensoy, the attackers primarily carried out adversary-in-the-middle attacks against specific targets. These operations involved planting loaders in predefined system locations and hosting encrypted malware components on attacker-controlled servers, which were delivered in response to manipulated DNS queries.
Evasive Panda’s use of DNS poisoning is not new. In April 2023, ESET reported that the group may have used similar techniques or a supply chain compromise to distribute trojanized versions of legitimate applications such as Tencent QQ during an attack on an international NGO in Mainland China. Later, in August 2024, Volexity revealed that the same threat actor compromised an unnamed internet service provider to push malicious software updates through DNS manipulation.
The group is part of a broader ecosystem of China-aligned threat actors that leverage adversary-in-the-middle techniques. ESET recently disclosed that it is monitoring at least ten active Chinese threat groups using DNS poisoning for initial access or lateral movement, including LuoYu, BlackTech, TheWizards APT, Blackwood, PlushDaemon, and FontGoblin.
In the campaigns analyzed by Kaspersky, Evasive Panda used fake software updates as infection lures. One such case involved a malicious update masquerading as software for SohuVA, a video streaming service operated by the Chinese company Sohu. The update was delivered through the domain p2p.hd.sohu.com[.]cn, strongly suggesting DNS manipulation.
Şensoy explained that the attackers likely altered DNS responses so that requests for the legitimate SohuVA update server were redirected to infrastructure under their control. Similar fake updater campaigns were also identified for Baidu’s iQIYI Video, IObit Smart Defrag, and Tencent QQ.
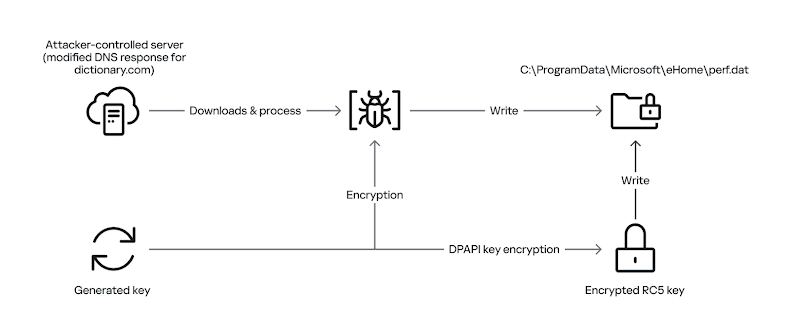
Once the initial loader was executed, it launched shellcode that retrieved an encrypted second-stage payload disguised as a PNG image. This payload was delivered through another DNS poisoning attack targeting the legitimate website dictionary[.]com. Victim systems were redirected to attacker-controlled IP addresses based on their geographic location and internet service provider.
While the exact method used to poison DNS responses remains unclear, Kaspersky suspects that either victim ISPs were selectively compromised or network devices such as routers or firewalls were breached.
The malware delivery process also included collecting the Windows version from infected systems, allowing attackers to tailor payloads for specific operating system environments. The final payload was decrypted and injected into a legitimate svchost.exe process, resulting in the deployment of an MgBot variant.
MgBot is a modular backdoor capable of stealing files, logging keystrokes, capturing clipboard data, recording audio, and harvesting browser credentials. These capabilities allow attackers to maintain long-term, stealthy access to compromised systems.
Kaspersky concluded that the campaign highlights Evasive Panda’s continued evolution, demonstrating advanced evasion techniques and a strong focus on persistence in high-value targets.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


