Cybersecurity analysts have uncovered a JavaScript based command and control framework known as PeckBirdy, which has been actively used by China-aligned advanced persistent threat groups since 2023 to compromise diverse environments.
According to research published by Trend Micro, the framework has been deployed in attacks against Chinese online gambling platforms as well as targeted operations aimed at Asian government institutions and private sector organizations.
Researchers Ted Lee and Joseph C Chen explained that PeckBirdy is implemented using JScript, an older scripting language, despite offering advanced functionality. This design choice allows the framework to operate across multiple execution contexts by abusing living off the land binaries, commonly referred to as LOLBins.
Trend Micro first identified PeckBirdy in 2023 after detecting malicious script injections on several Chinese gambling websites. These injected scripts were designed to retrieve and execute secondary payloads remotely, enabling attackers to deliver JavaScript based malware directly to victims.
The final objective of this activity involved presenting victims with fake Google Chrome software update pages. Users were deceived into downloading fraudulent update files, which resulted in malware installation. This campaign has been tracked under the name SHADOW-VOID-044.
SHADOW-VOID-044 is one of two intrusion clusters linked to PeckBirdy. The second campaign, named SHADOW-EARTH-045, was first observed in July 2024 and focused on Asian government agencies and private organizations, including an educational institution in the Philippines. In these incidents, attackers injected PeckBirdy links into legitimate government websites, likely to deploy credential harvesting scripts.
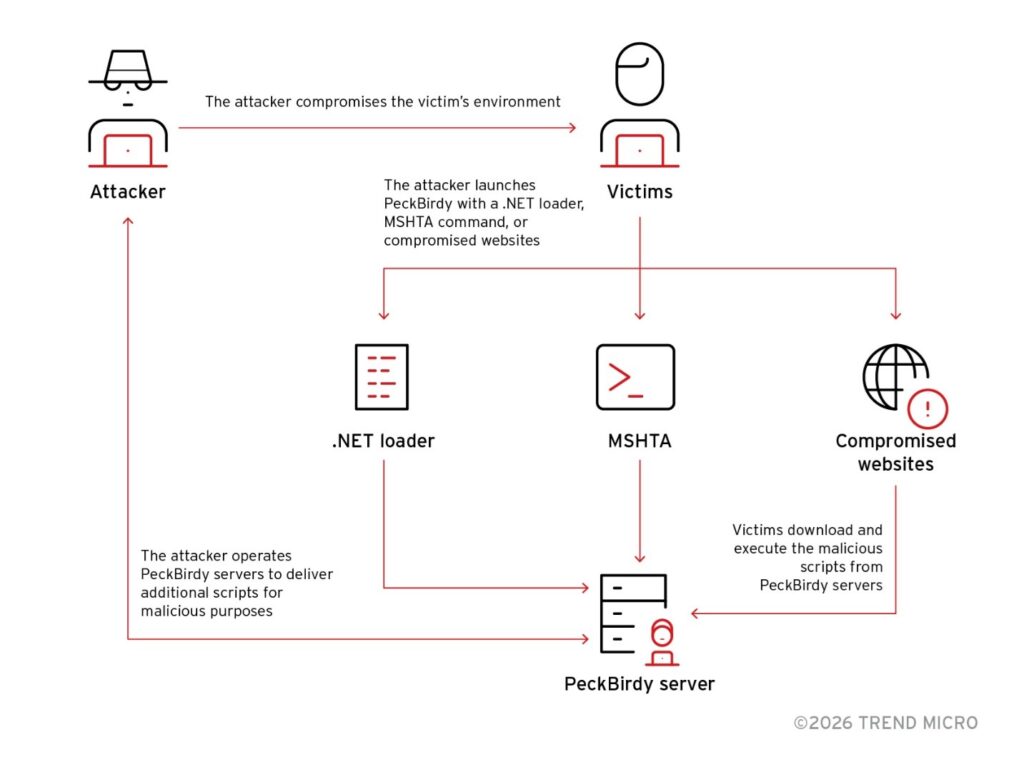
In one confirmed case, malicious code was embedded within a government system login page. In another, attackers leveraged MSHTA to execute PeckBirdy as a remote access channel to support lateral movement within a private organization. Trend Micro also observed the use of a custom .NET loader that launched PeckBirdy via ScriptControl, highlighting the framework’s adaptability.
PeckBirdy stands out due to its ability to operate across multiple platforms and execution methods, including web browsers, MSHTA, WScript, Classic ASP, Node.js, and .NET environments. Its server infrastructure supports multiple APIs that dynamically deliver environment specific scripts through HTTP or HTTPS requests.
Each API request contains a unique ATTACK ID, a predefined 32 character string that determines which PeckBirdy script is retrieved. Once executed, the framework identifies the execution environment, generates a persistent victim identifier, and stores it for future sessions.
Following initialization, PeckBirdy evaluates available communication channels. WebSocket is the primary protocol used for server communication, with fallback options including Adobe Flash ActiveX objects and Comet techniques when required.
After establishing contact with its command server and submitting both the ATTACK ID and victim ID, the server responds with a second stage payload. Some of these scripts are capable of stealing website cookies. One PeckBirdy server associated with SHADOW-VOID-044 was found hosting additional malicious components, including:
- Exploit code targeting a Google Chrome V8 vulnerability, CVE-2020-16040
- Social engineering scripts designed to trick users into executing malware
- Backdoor delivery scripts executed through Electron.js
- Reverse shell payloads using TCP socket connections
Further investigation uncovered two modular backdoors named HOLODONUT and MKDOOR. HOLODONUT is a .NET based backdoor deployed using a lightweight downloader called NEXLOAD and supports dynamic plugin management. MKDOOR offers similar modular capabilities, allowing modules to be loaded, executed, or removed on demand.
Researchers believe SHADOW-VOID-044 and SHADOW-EARTH-045 are likely operated by different China-linked threat actors. This conclusion is based on multiple indicators, including the presence of the GRAYRABBIT backdoor associated with UNC3569, infrastructure overlaps with WizardNet and TheWizards group, and similarities between MKDOOR and BIOPASS RAT, which has been attributed to Earth Lusca.
Additional evidence includes the use of infrastructure previously linked to Earth Baxia and APT41, reinforcing the assessment of nation state involvement.
Trend Micro concluded that these campaigns demonstrate how dynamic JavaScript frameworks like PeckBirdy can evade traditional security tools. Runtime generated code, lack of persistent artifacts, and abuse of trusted system binaries significantly complicate detection efforts for endpoint defenses.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


