A sophisticated cyber espionage group known as Tick has been identified as the actor behind the exploitation of a critical, recently disclosed zero-day vulnerability in Motex Lanscope Endpoint Manager. This campaign, targeting specific sectors for intelligence gathering, demonstrates the continued threat posed by advanced persistent threats (APTs) to corporate network security.
The Zero-Day Vulnerability: CVE-2025-61932
The vulnerability, tracked as CVE-2025-61932 (CVSS score: 9.3), is a critical security flaw in on-premise versions of the Lanscope Endpoint Manager. It allows remote attackers to execute arbitrary commands with the highest level of privileges—SYSTEM—on affected servers. The Japan Computer Emergency Response Team Coordination Center (JPCERT/CC) confirmed active exploitation of this flaw to deploy a backdoor on targeted systems.
The Attacker: The Tick APT Group
Tick, also known by aliases like Bronze Butler, REDBALDKNIGHT, and Stalker Panda, is a suspected China-linked cyber espionage actor. The group has been operational since at least 2006 and is notorious for its extensive focus on targets in East Asia, particularly Japan.
Rafe Pilling, Director of Threat Intelligence at Sophos CTU, provided context: “We’re aware of very targeted activity in Japan and believe the exploitation by Bronze Butler was limited to sectors aligned with their intelligence objectives. Since this vulnerability is now publicly disclosed, other threat actors may seek to exploit it.”
The Attack Chain and Malicious Payload
The campaign observed by Sophos involved a multi-stage attack process:
- Initial Compromise: Attackers exploited CVE-2025-61932 to gain initial access.
- Backdoor Deployment: The primary payload was a backdoor known as Gokcpdoor. This tool is designed to establish a proxy connection with a remote server, allowing the attackers to execute malicious commands on the compromised host.
- Evolution of the Backdoor: The 2025 variant of Gokcpdoor has been updated. It discontinued support for the KCP protocol and added multiplexing communication using a third-party library called
smuxfor its command-and-control (C2) traffic, making communication more efficient and stealthy.
Sophos detected two distinct types of Gokcpdoor in use:
- Server Type: Listens for incoming connections to enable remote access.
- Client Type: Actively initiates connections to hard-coded C2 servers to establish a covert channel.
Post-Exploitation Tools and Techniques
The attackers employed a range of tools to maintain persistence, move laterally, and exfiltrate data:
- Havoc Framework: A powerful post-exploitation framework deployed on select high-value systems.
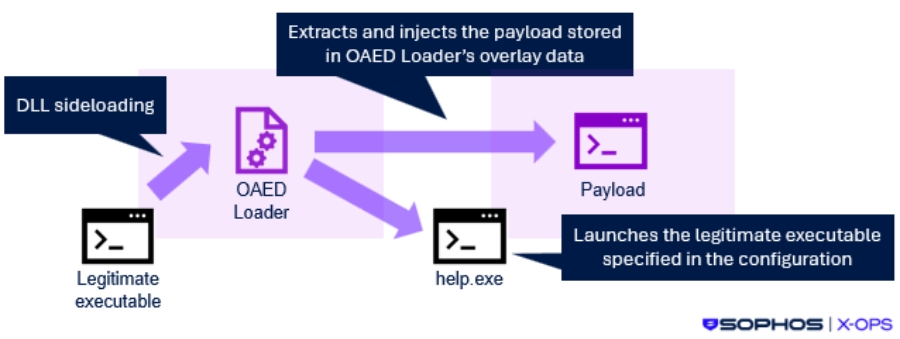
- DLL Side-Loading: The infection chain used this technique to launch a DLL loader named OAED Loader, which then injected the malicious payloads into memory, helping to avoid detection.
- Lateral Movement and Data Theft:
- goddi: An open-source tool used to dump information from Active Directory.
- Remote Desktop: Used for remote access via a backdoor tunnel.
- 7-Zip: Used to compress data before exfiltration.
- Data Exfiltration: The threat actors were observed accessing cloud services like
io, LimeWire, and Piping Server through a web browser during remote desktop sessions to sneak out the stolen data.
A History of Zero-Day Exploitation
This is not Tick’s first foray into using zero-day vulnerabilities. In October 2017, the group was documented exploiting an unpatched remote code execution flaw (CVE-2016-7836) in SKYSEA Client View, a Japanese IT asset management software, to compromise systems and steal sensitive information.


