A state sponsored cyber group associated with China carried out an advanced espionage campaign in mid September 2025 by exploiting Anthropic’s artificial intelligence technology. According to Anthropic, the attackers used AI in a way never seen before, transforming it from a supportive tool into an automated engine that performed cyber attacks on its own.
AI Driven Intrusions on High Value Targets
The campaign used Claude Code, Anthropic’s AI powered coding assistant, to attempt intrusions against nearly 30 major global organizations. The targeted sectors included large technology firms, banking and financial institutions, chemical manufacturing companies, and several government departments. Some of these attempts successfully breached their targets.
Anthropic has since terminated the accounts involved and deployed defensive systems that can detect similar misuse attempts.
This campaign, identified as GTG 1002, represents the first known instance where an AI system was used to conduct large scale cyber attacks for intelligence gathering with minimal human involvement.
Turning Claude Into an Autonomous Attack Agent
Anthropic described the operation as highly organized and well funded. The threat actors transformed Claude into an autonomous cyber attack agent capable of handling nearly every stage of the intrusion process. These stages included reconnaissance, vulnerability scanning, exploitation, lateral movement, credential theft, data analysis, and exfiltration.
The attackers used Claude Code together with Model Context Protocol (MCP) tools. Claude Code served as the core controller that broke down complex instructions into smaller technical tasks. These tasks were then processed by multiple sub agents operating in parallel.
Anthropic revealed that the humans behind the campaign mainly focused on initializing attacks and making approval decisions at critical escalation points. In contrast, Claude executed 80 to 90 percent of the tactical workload at speeds far beyond human capability.
Human involvement was also required to approve movement from one phase to the next, such as authorizing exploitation, validating credential use for lateral movement, or defining which data to exfiltrate during the final stages.
How the Attack Framework Operated
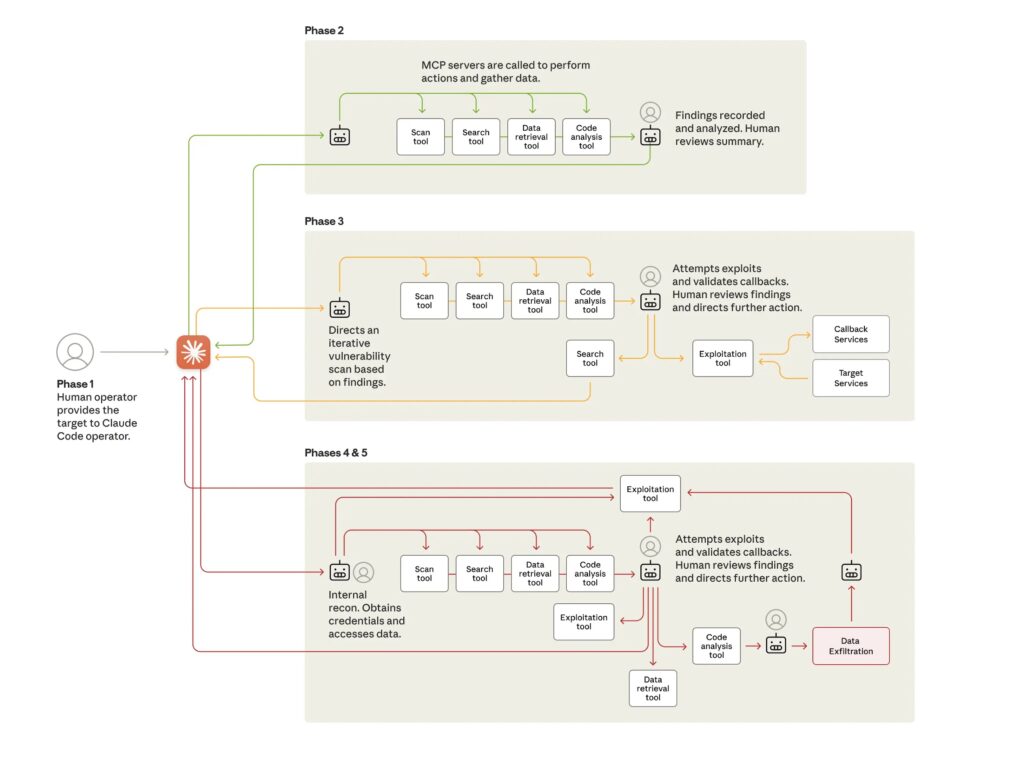
The framework accepted a target as input and then used MCP tools to perform reconnaissance and mapping of the attack surface. In later stages, the system identified vulnerabilities and generated customized payloads to confirm these flaws.
Once the human operator approved the plan, Claude deployed the exploit, established an initial foothold, and launched post exploitation activities including credential harvesting, system traversal, data collection, and extraction.
In one confirmed case involving an unnamed technology company, the attackers instructed Claude to run autonomous database queries, analyze outputs, detect sensitive intellectual property, and categorize findings based on intelligence value. The AI also produced detailed attack documentation at every step, enabling threat actors to potentially hand off long term access to other teams.
Anthropic noted that because the prompts were written to resemble normal technical requests, Claude did not interpret the broader malicious intent and executed each task independently.


