Threat actors believed to be linked to China have repurposed a legitimate open-source monitoring framework, Nezha, to conduct a coordinated cyberattack, researchers found. The campaign, observed in August 2025 by Huntress, used a log poisoning technique to plant a PHP web shell on vulnerable web servers, then leveraged that access to deploy Nezha and ultimately load Gh0st RAT, a remote access Trojan commonly associated with Chinese threat groups.
How the intrusion unfolded
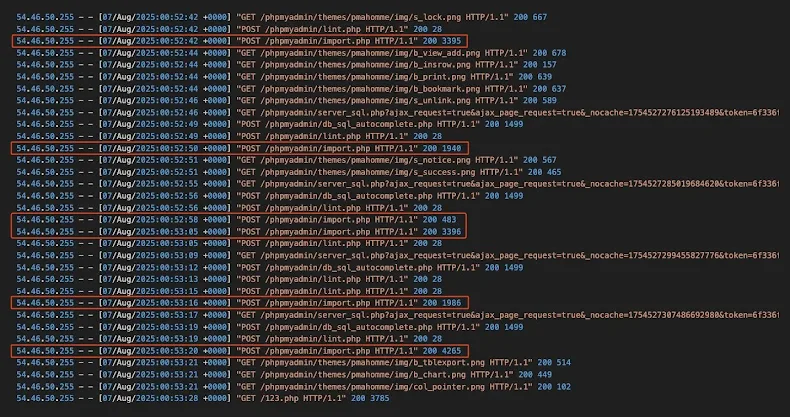
According to Huntress, attackers first gained initial access by exploiting a publicly exposed, vulnerable phpMyAdmin panel. They changed the panel language to simplified Chinese, then used the server’s SQL query interface to run a series of quick SQL commands. Those queries were crafted to be written into the server’s query log, after which the attackers set the log file name with a .php extension. One of the logged queries contained a compact PHP web shell, which, because of the .php extension, could be executed directly by sending POST requests to the server.
With the web shell active, the operators used ANTSWORD, a web shell management tool, to run commands on the server, for example, the whoami command to check privileges. From there, they delivered the Nezha agent, an open-source operations and monitoring tool, which connected back to an external command server identified as c.mid[.]al, enabling remote control of the compromised host.
Scope, geographic spread, and actor details
Huntress reports that the campaign likely affected over 100 machines. Most infections were concentrated in Taiwan, Japan, South Korea, and Hong Kong. Smaller clusters of victims were identified in Singapore, Malaysia, India, the U.K., the U.S., Colombia, Laos, Thailand, Australia, Indonesia, France, Canada, Argentina, Sri Lanka, the Philippines, Ireland, Kenya, and Macao. The attackers operated a Nezha dashboard that, unusually, displayed its interface in Russian, and listed more than 100 victims worldwide.
Malware and post-compromise activity
After Nezha was installed, operators executed an interactive PowerShell script that created exclusions in Microsoft Defender Antivirus, then launched Gh0st RAT. The RAT was run via a loader and dropper sequence, which configured and started the main payload. This combination allowed remote command execution, data theft, and long-term persistence on compromised systems.
Why this matters, and lessons learned
Researchers emphasized that the campaign illustrates how threat actors increasingly abuse legitimate, publicly available tools for malicious ends. Open-source tooling is attractive because it reduces development cost, offers plausible deniability compared to custom malware, and can evade detection by security products. The use of log poisoning to convert a server log into an executable web shell is a reminder that logging mechanisms and exposed management panels, such as phpMyAdmin, must be carefully secured and monitored.


