According to an analysis by Proofpoint, the intrusions impersonated senior figures and organizations involved in U.S.-China relations, including the Chair of the Select Committee on Strategic Competition between the United States and the Chinese Communist Party, and the U.S.-China Business Council. The emails specifically targeted people working on trade, economic policy, and bilateral relations, implying an intelligence collection objective linked to ongoing U.S.-China trade negotiations.
Timing and attribution
Proofpoint observed this activity throughout July and August, 2025, and assessed it as likely driven by Chinese state aligned actors. The researchers noted overlaps between TA415 and historically tracked clusters such as APT41 and Brass Typhoon, sometimes referenced as Barium. These findings followed a U.S. House Select Committee on China advisory, which warned of ongoing targeted campaigns that included impersonation of a U.S. congressman to distribute data stealing malware.
How the phishing worked
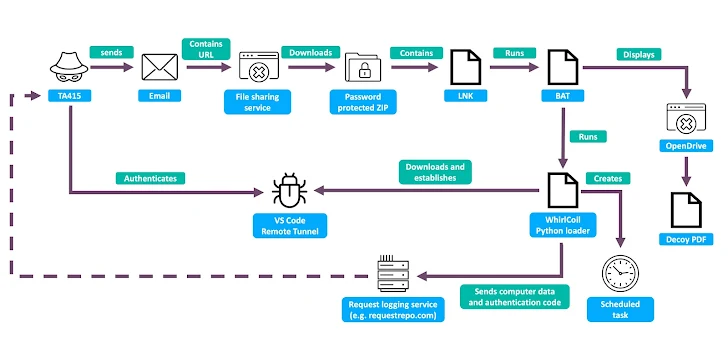
Victims received messages posing as invitations to a closed briefing on U.S.-Taiwan, and U.S.-China affairs, often spoofing the U.S.-China Business Council. The emails were sent from the address uschina@zohomail[.]com, and used Cloudflare WARP VPN to mask the source. Recipients were directed to password protected archives hosted on public cloud services, including Zoho WorkDrive, Dropbox, and OpenDrive. Inside those archives researchers found a Windows shortcut file, LNK, plus other files hidden in a concealed folder.
Infection chain and persistence
The LNK shortcut executed a batch script from the hidden folder, while simultaneously showing a decoy PDF to the user. The batch then launched an obfuscated Python loader dubbed WhirlCoil, included in the archive. Earlier variants downloaded the loader from paste hosting sites such as Pastebin, or directly fetched a Python package from the official Python site, Proofpoint said.
To maintain persistence, the script created a scheduled task, often named GoogleUpdate or MicrosoftHealthcareMonitorNode, set to run the loader every two hours. Where possible, the task was configured to run with SYSTEM privileges if the compromised user had administrative rights on the host.
VS Code remote tunnels used as backdoor
Once active, the Python loader established a Visual Studio Code remote tunnel, providing the threat actor with a persistent backdoor into the system. Through this tunnel, the attacker could access the file system and run arbitrary commands using the Visual Studio integrated terminal. The loader collected system metadata and harvested files from various user directories, then encoded the stolen data into base64 and exfiltrated it via HTTP POST requests to a free request logging service, for example requestrepo[.]com.
Campaign similarities to 2024 incidents
Proofpoint pointed out that this infection chain closely resembles a September, 2024 attack that targeted organizations in aerospace, chemicals, insurance, and manufacturing, where the Visual Studio Code Remote Tunnels mechanism was also used via a Python loader. The recurrence suggests the actor continues to refine a reliable toolset for long term access and data theft.
Implications and recommendations
The targeted nature of the campaign, combined with the use of legitimate services like cloud sharing platforms and VS Code remote tunnels, highlights the challenge of identifying sophisticated espionage that blends social engineering and developer tooling. Security teams should be cautious of unexpected archive or LNK attachments, verify sources of invites, monitor for unusual scheduled tasks with names similar to legitimate update services, and restrict unnecessary usage of developer remote access features. Forensic review of endpoints for indicators such as the WhirlCoil loader, scheduled tasks named GoogleUpdate or MicrosoftHealthcareMonitorNode, and outbound calls to requestrepo[.]com can help detect kompromat gathered through this technique.