Cybersecurity researchers have discovered a cluster of malicious Google Chrome extensions designed to hijack affiliate links, exfiltrate user data, and steal OpenAI ChatGPT authentication tokens. These extensions exploit the trust users place in popular e-commerce and AI-related browser tools to gain persistent access to sensitive information.
Amazon Ads Blocker and Affiliate Hijacking
One notable extension, Amazon Ads Blocker (ID: pnpchphmplpdimbllknjoiopmfphellj), claims to block ads on Amazon for a cleaner browsing experience. Released on January 19, 2026, by the publisher 10Xprofit, the extension quietly replaces affiliate codes in all Amazon product links with the developer’s code, 10xprofit-20, effectively diverting commissions from legitimate content creators.
Socket Security researcher Kush Pandya explained, “The extension blocks ads as advertised, but its hidden purpose is automatic affiliate tag injection and replacement of existing codes, giving the developer illicit earnings.”
Broader Extension Cluster
Further investigation revealed that Amazon Ads Blocker is part of a network of 29 extensions targeting platforms such as Amazon, AliExpress, Best Buy, Shein, Shopify, and Walmart. These extensions include:
- AliExpress Invoice Generator, AliExpress Price Tracker, AliExpress Quick Currency Converter
- Amazon Seller Tools, ASIN Lookup, Product Scraper, Price History Saver, Keyword Tools
- BestBuy Search By Image, SHEIN Search By Image, Shopify Search By Image, Walmart Search By Image
These extensions scan all URLs for existing affiliate tags and either replace them with attacker-controlled codes or append new tags if none exist. Some also manipulate AliExpress product pages with fake “LIMITED TIME DEAL” timers to trick users into making purchases, maximizing stolen commissions.
Policy Violations
The extensions violate Chrome Web Store policies:
- Misleading disclosures about affiliate commissions
- Replacement of user or content creator affiliate codes without consent
- Combining unrelated functions (e.g., ad blocking and affiliate injection) in a single extension
Socket researchers warn that such behavior undermines user consent and presents a high-risk threat, particularly when mixed with price comparison or coupon features.
ChatGPT Token Theft Extensions
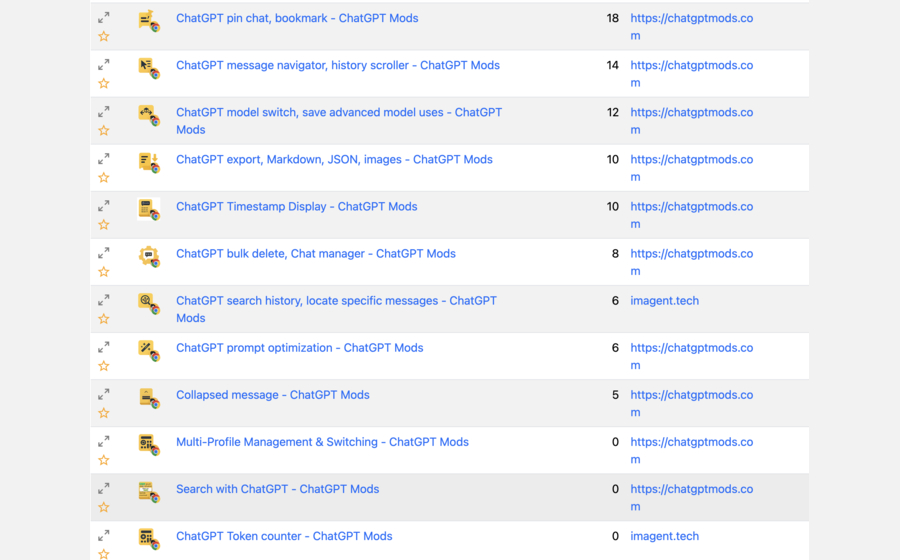
A separate network of 16 malicious extensions (15 on Chrome, 1 on Edge) targets ChatGPT authentication tokens by injecting scripts into chatgpt.com. LayerX reports indicate these extensions were downloaded roughly 900 times and share overlapping source code, branding, and descriptions, suggesting a coordinated campaign. Some extensions include:
- ChatGPT Mods: Folder/Voice Download, Prompt Manager, Bulk Delete, Model Switching, Export Tools
- ChatGPT Timestamp Display, Token Counter, Multi-Profile Management
Possession of these tokens allows attackers full account access, including conversation history, saved prompts, and metadata. Attackers can impersonate the user and access all data without additional credentials.
Emerging Browser Exploit Surface
As AI and e-commerce browser extensions become integral to workflows, malicious actors are exploiting the elevated permissions of these tools to steal sensitive data. According to Symantec and Varonis researchers, browser extensions are now a primary attack vector in enterprise environments, particularly with BYOD policies, remote work, and SaaS usage.
Malware-as-a-Service: Stanley
A related development involves Stanley, a malware-as-a-service kit sold on Russian cybercrime forums for $2,000–$6,000. The toolkit allows criminals to create Chrome extensions that:
- Inject phishing pages via full-screen iframes while keeping the URL bar legitimate
- Collect credentials from banking or targeted websites
- Manage victims through a C2 panel and configure spoofed redirects
Although Stanley reportedly disappeared after the January 2026 public disclosure, experts warn it could resurface under a new name.
Varonis researcher Daniel Kelley commented, “Chrome extensions have become a strategic attack surface. The combination of trust, elevated permissions, and user reliance makes them highly effective for cybercriminal campaigns.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


