Cybersecurity researchers have uncovered two malicious Google Chrome extensions operating under the same name and published by the same developer, both designed to secretly intercept web traffic and steal user credentials on a massive scale.
The extensions are promoted as a “multi location network speed test plug in” aimed at developers and professionals working in foreign trade. At the time of discovery, both extensions remained available for download on the Chrome Web Store.
The identified extensions are:
Phantom Shuttle, Extension ID fbfldogmkadejddihifklefknmikncaj, with approximately 2,000 users, published on November 26, 2017
Phantom Shuttle, Extension ID ocpcmfmiidofonkbodpdhgddhlcmcofd, with around 180 users, published on April 27, 2023
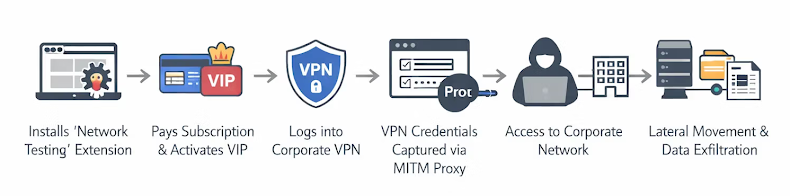
According to Socket security researcher Kush Pandya, users are charged subscription fees ranging from 9.9 to 95.9 Chinese Yuan, believing they are purchasing a legitimate VPN style service. In reality, both versions of the extension perform identical malicious activities in the background.
Researchers revealed that the extensions conduct full traffic interception by injecting authentication credentials, operating as man in the middle proxies, and continuously exfiltrating sensitive user data to a command and control server controlled by the threat actor.
Once users complete payment, they are granted VIP status. At that point, the extension automatically activates a feature known as “smarty” proxy mode, which reroutes traffic from more than 170 targeted domains through attacker controlled infrastructure.
Despite their malicious purpose, the extensions appear to function as advertised. They conduct real latency tests, display proxy connection status, and provide feedback that convinces users the service is legitimate. This behavior is designed to conceal the real objective, which is large scale credential harvesting.
The malicious functionality is implemented through modified JavaScript files embedded within the extension, including jquery 1.12.2 and scripts.js. These scripts register a listener using chrome.webRequest.onAuthRequired, allowing the extension to silently inject hard coded proxy credentials into every HTTP authentication request.
Whenever a website or service requests authentication, including basic authentication, digest authentication, or proxy authentication, the listener responds instantly with preset credentials without alerting the user. This process occurs synchronously, ensuring no user interaction is required.
After proxy authentication is established, the extension modifies Chrome’s proxy settings using a Proxy Auto Configuration (PAC) script. This script supports three operating modes.
The close mode disables proxy functionality entirely.
The always mode routes all browsing traffic through the proxy.
The smarty mode selectively routes traffic from a predefined list of more than 170 high value domains.
The targeted domains include developer platforms such as GitHub, Stack Overflow, and Docker, cloud service providers like Amazon Web Services, DigitalOcean, and Microsoft Azure, enterprise vendors including Cisco, IBM, and VMware, as well as social media platforms and adult content websites. Researchers believe the inclusion of adult sites may be intended for blackmail or coercion.
As a result, all affected traffic passes through attacker controlled proxy servers. The extension also maintains a recurring heartbeat connection to its command and control server at phantomshuttle[.]space, which remains active. This setup allows attackers to monitor sessions, manipulate traffic, and inject malicious payloads.
More critically, the heartbeat communication transmits VIP user data every five minutes using an HTTP GET request. The leaked information includes email addresses, plaintext passwords, and extension version details, enabling continuous credential theft and session tracking.
Security analysts warn that this combination of real time traffic interception and persistent credential exfiltration gives attackers extensive access to sensitive data. This includes login credentials, credit card details, authentication cookies, browsing history, form submissions, API keys, and access tokens. The compromise of developer credentials also raises the risk of downstream supply chain attacks.
While the individuals behind the operation have not been identified, multiple indicators suggest a China based origin. These include Chinese language usage in extension descriptions, integration of Alipay and WeChat Pay for subscriptions, and hosting of the command and control infrastructure on Alibaba Cloud.
Researchers noted that the paid subscription model helps retain victims while generating revenue, and the professional payment setup creates a convincing appearance of legitimacy. Users believe they are installing a VPN tool while unknowingly granting attackers full visibility into their online activity.
The findings underscore the growing security risks posed by browser extensions, particularly in enterprise environments. Users who have installed these extensions are strongly advised to remove them immediately. Security teams are encouraged to enforce strict extension allowlisting, monitor extensions that request proxy permissions alongside payment systems, and watch for abnormal proxy authentication behavior across networks.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


