The United States Cybersecurity and Infrastructure Security Agency (CISA) has expanded its Known Exploited Vulnerabilities (KEV) catalog by adding a cross-site scripting flaw that affects OpenPLC ScadaBR on both Windows and Linux systems. The decision follows confirmed evidence that the vulnerability is being actively used by attackers.
The flaw, tracked as CVE-2021-26829 with a CVSS score of 5.4, is present in system_settings.shtm. It impacts the following software versions:
• OpenPLC ScadaBR through version 1.12.4 on Windows
• OpenPLC ScadaBR through version 0.9.1 on Linux
This addition comes shortly after an investigation revealed that a pro Russian hacktivist group named TwoNet attempted to compromise a Forescout honeypot in September 2025. The attackers reportedly believed the honeypot was a real water treatment facility.
During the incident, TwoNet shifted from initial access to disruptive activity in nearly 26 hours. They used default credentials to enter the system, performed reconnaissance, and created a new user account named BARLATI to maintain persistence. The group later exploited CVE-2021-26829 to alter the HMI login page by adding a pop up message that stated Hacked by Barlati. They also changed settings to disable logs and alarms while being unaware that the target was a controlled testing environment.
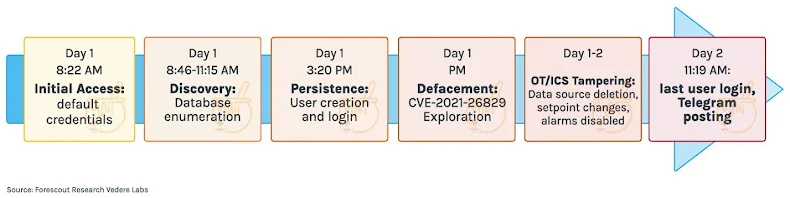
According to Forescout, the attackers did not attempt to escalate privileges or compromise the underlying host. Their actions remained limited to the web application layer of the HMI.
TwoNet began operating on Telegram in January 2025. The group initially engaged in distributed denial of service activity, then expanded into broader operations involving industrial system attacks, doxxing, ransomware as a service, hack for hire services, and initial access sales. They have also claimed connections with other hacktivist identities including CyberTroops and OverFlame.
Federal Civilian Executive Branch agencies must apply the required patches before December 19, 2025.
OAST Activity Drives Exploit Attempts
In a related development, VulnCheck reported a long running Out of Band Application Security Testing endpoint hosted on Google Cloud that is being used to conduct region specific exploit attempts. The activity is currently aimed at Brazil.
Jacob Baines, CTO at VulnCheck, stated that their sensors recorded nearly 1,400 exploit attempts across more than 200 CVEs originating from this infrastructure. While the activity resembles typical Nuclei template scans, the attacker infrastructure, payload style, and geographic targeting appear unusual.
The attacker workflow involves exploiting a vulnerability and then triggering an HTTP request to one of their OAST subdomains under the pattern *.i sh.detectors testing[.]com. These callbacks have been active since at least November 2024.
The exploit attempts appear to originate from Google Cloud hosted systems in the United States. This indicates that malicious actors are actively abusing legitimate cloud services to avoid detection and blend with regular traffic.
VulnCheck also found a Java class file named TouchFile.class on the IP address 34.136.22[.]26 which is linked to the OAST domain. The file enhances a public Fastjson remote code execution exploit by introducing command execution and outbound HTTP request features.
According to Baines, the longevity of the OAST setup and the consistent targeting pattern suggest an actor engaged in sustained scanning rather than short term or opportunistic probing.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


