The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has disclosed the use of a sophisticated backdoor, BRICKSTORM, by state-sponsored Chinese threat actors to maintain long-term access to compromised systems across the United States.
CISA described BRICKSTORM as a highly advanced implant designed for VMware vSphere and Windows environments. It allows attackers to gain stealthy access, execute commands, and maintain persistent control over the affected systems. Written in Golang, the malware provides an interactive shell, enabling operators to browse, upload, download, create, delete, and manipulate files.
The malware primarily targets government agencies and IT sectors. It supports multiple communication methods, including HTTPS, WebSockets, nested TLS, and DNS-over-HTTPS (DoH) to hide activity. It can also function as a SOCKS proxy for lateral network movement.
The agency did not specify the number of affected organizations or the data compromised. These attacks reflect ongoing tactical evolution by Chinese hacking groups, increasingly targeting edge network devices and cloud infrastructure.
A statement from the Chinese embassy in Washington rejected the claims, denying any government involvement in cyberattacks.
BRICKSTORM was first reported by Google Mandiant in 2024, linked to zero-day exploitation of Ivanti Connect Secure vulnerabilities (CVE-2023-46805 and CVE-2024-21887). CrowdStrike has connected the malware to two clusters: UNC5221 and Warp Panda, a new China-linked adversary.
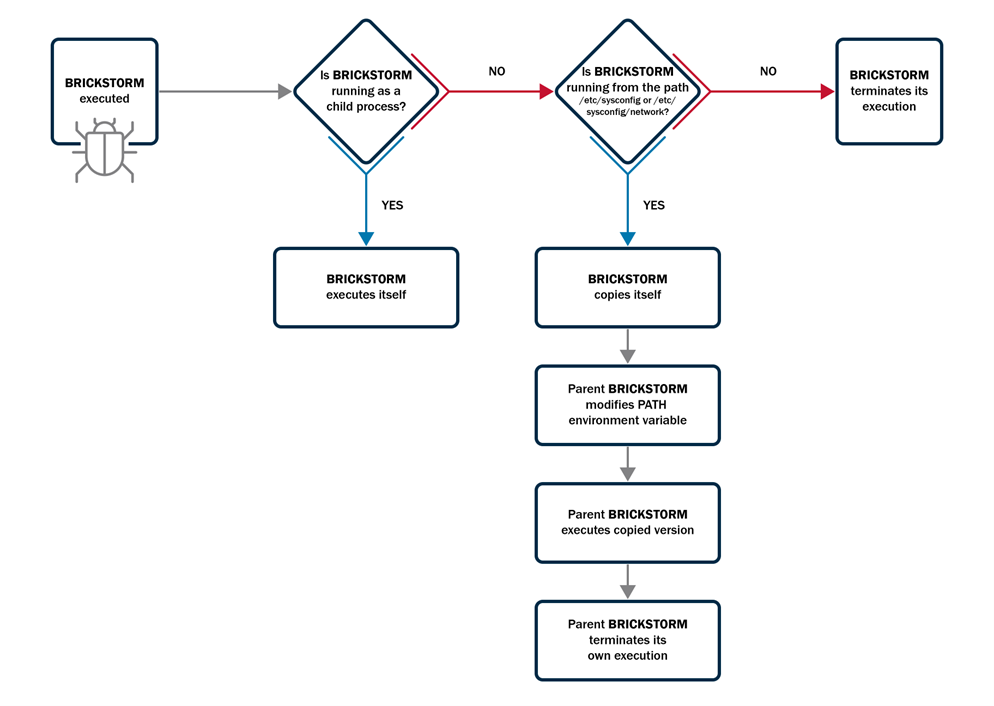
Earlier this year, Mandiant and Google Threat Intelligence observed attacks on U.S.-based legal, SaaS, BPO, and technology firms using BRICKSTORM. One key feature of the malware is its self-monitoring function, allowing automatic reinstallation or restart to maintain persistence.

In April 2024, attackers reportedly accessed a web server in an organization’s DMZ using a web shell, later moving to a VMware vCenter server to deploy BRICKSTORM. They obtained service account credentials and moved laterally via RDP to capture Active Directory information. Attackers also leveraged SMB to jump to additional servers and exfiltrate cryptographic keys, using vCenter privileges to finalize the BRICKSTORM deployment.
CISA notes BRICKSTORM uses custom handlers to set up SOCKS proxies, create web servers on infected machines, and execute commands. Some components are designed for virtualized environments, utilizing virtual sockets (VSOCK) for inter-VM communication, data exfiltration, and persistence.
Warp Panda Deploys BRICKSTORM Against U.S. Entities
CrowdStrike reported that Warp Panda has conducted multiple intrusions targeting VMware vCenter environments in legal, technology, and manufacturing sectors in the U.S., deploying BRICKSTORM along with two additional Golang implants, Junction and GuestConduit. Junction acts as an HTTP server facilitating commands, network proxying, and VM communication, while GuestConduit tunnels network traffic between guest VMs and hypervisors via VSOCK.
Initial access is achieved through internet-facing edge devices, using valid credentials or exploiting vCenter vulnerabilities. Lateral movement involves SSH, vCenter management accounts, and SFTP for data transfer.
Some exploited vulnerabilities include:
- CVE-2024-21887 (Ivanti Connect Secure)
- CVE-2023-46805 (Ivanti Connect Secure)
- CVE-2024-38812 (VMware vCenter)
- CVE-2023-34048 (VMware vCenter)
- CVE-2021-22005 (VMware vCenter)
- CVE-2023-46747 (F5 BIG-IP)
The attackers maintain stealth through log clearing, timestomping, and using temporary rogue VMs. They also clone domain controller VMs and access employee email accounts relevant to Chinese government interests.
Warp Panda has targeted cloud environments, accessing Microsoft Azure, OneDrive, SharePoint, and Exchange data. They reportedly used session replay attacks via BRICKSTORM implants to obtain Microsoft 365 access and downloaded sensitive SharePoint files. Persistence methods also include registering new MFA devices and enumerating Microsoft Graph API objects such as service principals, applications, users, and emails.
CrowdStrike concluded that these persistent, covert intrusions likely serve PRC intelligence collection efforts targeting North American entities.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.