The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has officially confirmed that threat actors are actively exploiting critical security vulnerabilities in two widely used enterprise platforms: Dassault Systèmes’ DELMIA Apriso and the open-source XWiki. These flaws grant attackers the ability to execute arbitrary code and seize control of affected systems, prompting urgent calls for patching.
The Critical Vulnerabilities at a Glance
CISA has added these specific vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, mandating federal agencies to address them promptly. The flaws present a severe risk to organizational security.
- CVE-2025-6205 (CVSS: 9.1): A critical missing authorization flaw in Dassault DELMIA Apriso that allows an unauthenticated attacker to gain privileged application access.
- CVE-2025-6204 (CVSS: 8.0): A code injection vulnerability in the same Dassault product, enabling arbitrary code execution on the underlying server.
- CVE-2025-24893 (CVSS: 9.8): A critical eval injection vulnerability in XWiki that permits any guest user to achieve remote code execution via a specific endpoint (
/bin/get/Main/SolrSearch).
The Dassault DELMIA Apriso Threat Chain
The two Dassault vulnerabilities, affecting versions from 2020 through 2025, form a potent one-two punch. Researchers from ProjectDiscovery detailed how attackers can chain these flaws together for a complete system takeover.
The exploit chain works as follows:
- Attackers first abuse the authorization flaw (CVE-2025-6205) to create user accounts with elevated privileges.
- They then leverage the code injection bug (CVE-2025-6204) to upload and execute malicious files within a web-served directory.
This combination results in a full compromise of the DELMIA Apriso application. Dassault Systèmes released patches for these issues in early August 2025.
A Recurring Problem
This marks the second time in just over a month that CISA has flagged active attacks against the DELMIA Apriso platform. A previous critical flaw, CVE-2025-5086, was also added to the KEV catalog after exploitation was detected in the wild, raising questions about the scope of these ongoing campaigns.
XWiki Under Attack: A Stealthy Crypto-Miner Operation
Simultaneously, a critical vulnerability in XWiki (CVE-2025-24893) is being aggressively exploited in a calculated, two-stage attack to deploy cryptocurrency mining software.
According to VulnCheck, which first detected the exploitation, the attacks originate from an IP address in Vietnam (123.25.249[.]88). The process is deliberately slow to avoid detection.
The Two-Pass Attack Workflow
- First Pass: The attacker exploits the vulnerability to stage a downloader on the XWiki server, writing a file to the disk.
- Second Pass: After a delay of at least 20 minutes, a second exploit triggers the downloader, which retrieves the main payloads.
The payloads perform distinct functions:
- Payload
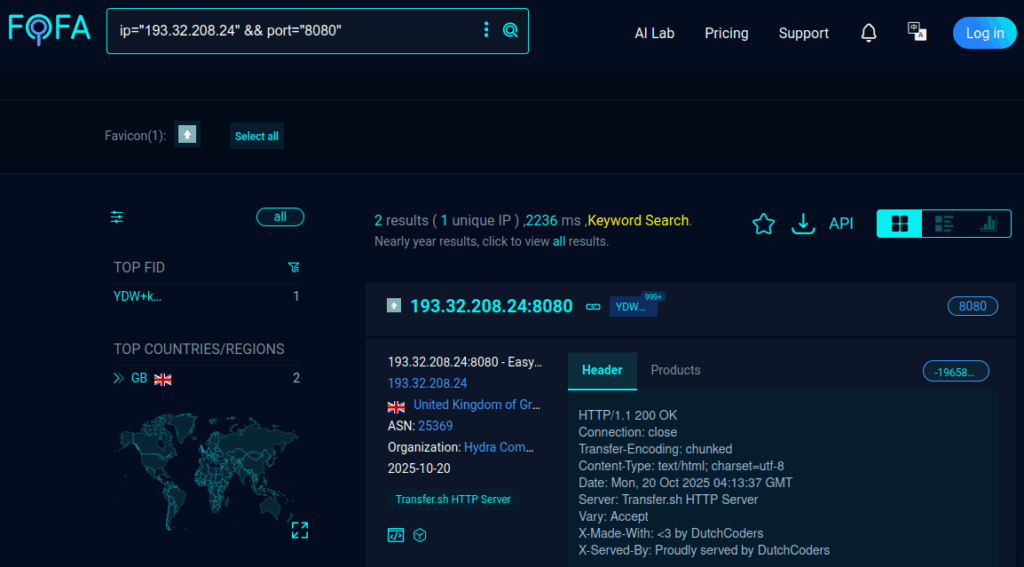
x521: Fetches the actual cryptocurrency miner from the attacker-controlled server193.32.208[.]24:8080. - Payload
x522: Acts as a “killer script,” terminating competing miners like XMRig and Kinsing to ensure maximum resource allocation for the attacker’s own miner, which is configured for the c3pool.org mining pool.


