The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent alert, adding a severe vulnerability found in WatchGuard Fireware to its Known Exploited Vulnerabilities (KEV) catalog after confirming active exploitation in the wild.
The flaw, tracked as CVE-2025-9242 with a CVSS score of 9.3, is an out-of-bounds write vulnerability affecting the following Fireware OS versions:
- 11.10.2 up to and including 11.12.4_Update1
- 12.0 up to and including 12.11.3
- 2025.1
According to CISA, “WatchGuard Firebox contains an out-of-bounds write vulnerability in the OS iked process that may allow a remote unauthenticated attacker to execute arbitrary code.”
Security researchers at watchTowr Labs uncovered the flaw last month, explaining that it originates from a missing length check in an identification buffer during the IKE handshake process. Researcher McCaulay Hudson elaborated that although the server performs certificate validation, the validation occurs after the vulnerable code executes, making the flaw exploitable before authentication.
Currently, there are no public details about how the vulnerability is being weaponized or the extent of its exploitation. However, data shared by the Shadowserver Foundation indicates that as of November 12, 2025, more than 54,300 Firebox devices remain exposed to potential attacks. This is a decrease from 75,955 vulnerable devices recorded on October 19.
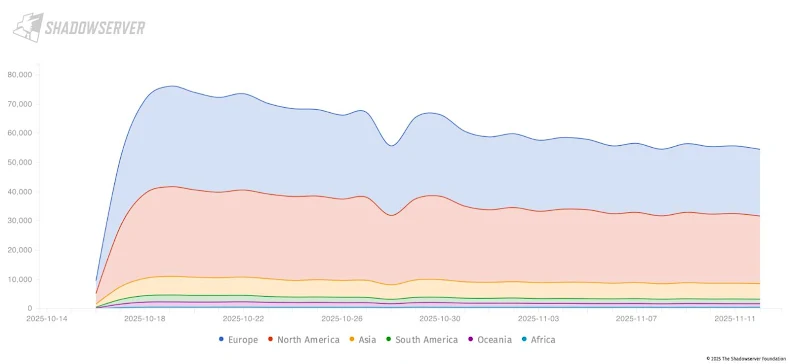
Geographically, the highest number of exposed devices are located in the United States (18,500), followed by Italy (5,400), the United Kingdom (4,000), Germany (3,600), and Canada (3,000).
CISA has directed all Federal Civilian Executive Branch (FCEB) agencies to deploy the latest WatchGuard patches no later than December 3, 2025, to mitigate potential threats.
In addition to this alert, CISA also listed two other vulnerabilities in the KEV catalog:
- CVE-2025-62215 (CVSS 7.0) – a newly discovered Windows kernel flaw
- CVE-2025-12480 (CVSS 9.1) – an improper access control vulnerability in Gladinet Triofox, actively exploited by a threat actor identified as UNC6485 by Google’s Mandiant Threat Defense team.


