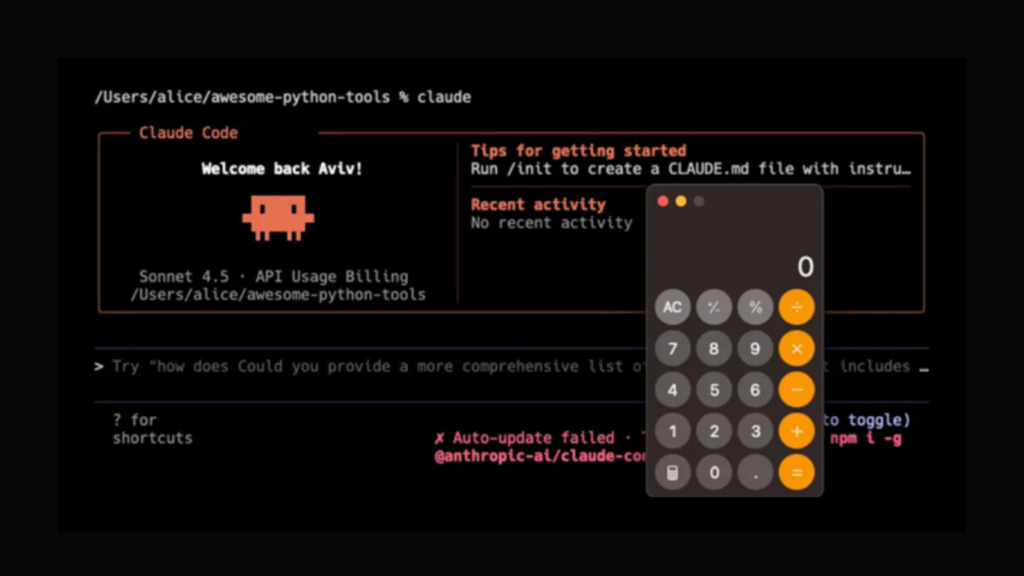
Cybersecurity researchers have revealed several critical security flaws in Anthropic’s Claude Code, an AI-driven coding assistant, which could allow attackers to execute remote code and steal API credentials.
Check Point researchers Aviv Donenfeld and Oded Vanunu reported, “These vulnerabilities exploit multiple configuration points, including Hooks, Model Context Protocol (MCP) servers, and environment variables. Attackers can execute arbitrary shell commands and exfiltrate Anthropic API keys when developers clone or open untrusted repositories.”
Overview of the Flaws
The discovered vulnerabilities fall into three main categories:
- No CVE (CVSS score: 8.7) – A code injection flaw occurs when Claude Code is launched in a new directory, bypassing user consent. Untrusted project hooks defined in
.claude/settings.jsoncould trigger arbitrary code execution. This was fixed in version 1.0.87 released in September 2025. - CVE-2025-59536 (CVSS score: 8.7) – This vulnerability allows automatic execution of shell commands if Claude Code is started in an untrusted directory. Exploitation occurs via repository-defined configurations in
.mcp.jsonand.claude/settings.json, potentially bypassing explicit user approval. Fixed in version 1.0.111 (October 2025). - CVE-2026-21852 (CVSS score: 5.3) – An information disclosure issue in the project-load workflow lets attackers exfiltrate sensitive data, including Anthropic API keys. This was addressed in version 2.0.65 (January 2026).
Anthropic explained, “If a repository sets ANTHROPIC_BASE_URL to an attacker-controlled endpoint, Claude Code may issue API requests before displaying the trust prompt, potentially exposing user API keys.”
Implications for Developers
Simply opening a crafted repository can compromise an active API key, redirect authenticated API traffic, and capture credentials. Attackers could then access shared project files, modify or delete cloud data, upload malicious content, and even generate unexpected API charges.
Successful exploitation of the first vulnerability may execute code silently on a developer’s machine without further interaction beyond opening the project.
Similarly, CVE-2025-59536 leverages repository-defined configuration files to override user permissions before interacting with external tools via MCP. By enabling the enableAllProjectMcpServers option, attackers can automate potentially harmful operations.
Check Point highlighted, “AI-powered development tools now treat configuration files as part of the execution layer. Operational context can directly influence system behavior, transforming the threat model. Risk extends beyond running untrusted code to opening untrusted projects, with supply chain threats originating not just from source code, but also automation layers.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.