Cybersecurity researchers have uncovered an advanced ClickFix campaign that combines deceptive CAPTCHA prompts with a signed Microsoft Application Virtualization (App-V) script to deliver a new information stealer known as Amatera.
According to findings published by Blackpoint researchers Jack Patrick and Sam Decker, the attackers deliberately avoid launching PowerShell directly. Instead, they abuse a trusted Microsoft script to control execution flow and evade traditional detection mechanisms. This technique allows malicious activity to blend in with legitimate system behavior.
Abuse of App-V as a Living-Off-the-Land Technique
At the core of the campaign is the misuse of SyncAppvPublishingServer.vbs, a signed Visual Basic Script that ships with Microsoft App-V. The attackers weaponize this script as a living-off-the-land binary, using it as a proxy to execute PowerShell commands indirectly via wscript.exe.
This approach helps attackers bypass PowerShell execution restrictions and security monitoring, since the activity appears to originate from a trusted Windows component. While similar abuse of this script was observed in 2022 by threat groups such as DarkHotel and BlueNoroff, this marks the first confirmed use of the technique in ClickFix-based attacks.
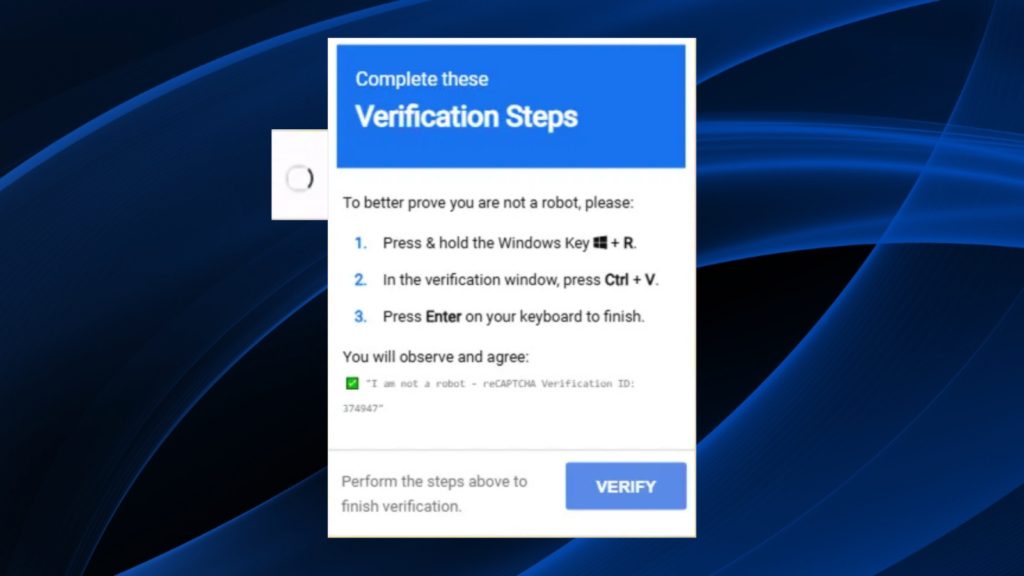
Fake CAPTCHA as the Initial Infection Vector
The attack begins with a fake CAPTCHA verification page that instructs users to copy and paste a command into the Windows Run dialog. Unlike traditional ClickFix campaigns, the pasted command does not directly call PowerShell. Instead, it invokes the App-V script, which then retrieves and executes a malicious loader entirely in memory.
This method relies heavily on user interaction, turning the victim into the initial access vector and making the activity appear legitimate to endpoint security tools.
Enterprise Systems as Primary Targets
App-V is only available on Enterprise and Education editions of Windows, as well as modern Windows Server versions. Systems running Windows Home or Pro are not affected, as the script fails to execute. This strongly suggests that enterprise-managed environments are the primary targets of the campaign.
Once executed, the obfuscated loader performs multiple checks to detect sandbox or analysis environments. It then retrieves configuration data from a public Google Calendar (ICS) file, effectively abusing a trusted third-party service as a dead drop resolver.
By externalizing configuration data in this way, attackers can rotate infrastructure or modify payload delivery without changing earlier stages of the attack chain, significantly increasing campaign longevity.
Multi-Stage Payload Delivery and Amatera Stealer
Parsing the calendar file leads to the retrieval of additional loader stages, including multiple PowerShell scripts executed directly in memory. The chain ultimately downloads PNG images from domains such as gcdnb.pbrd[.]co and iili[.]io, which secretly contain encrypted and compressed PowerShell payloads.
These payloads are decrypted and decompressed in memory before being executed, resulting in a shellcode loader that deploys Amatera Stealer.
Blackpoint researchers noted that the strength of the campaign lies not in a single technique, but in the careful chaining of multiple evasive methods. Each stage validates the previous one, ensuring execution only proceeds under expected conditions, which complicates automated analysis and sandbox detonation.
The Expanding ClickFix Ecosystem
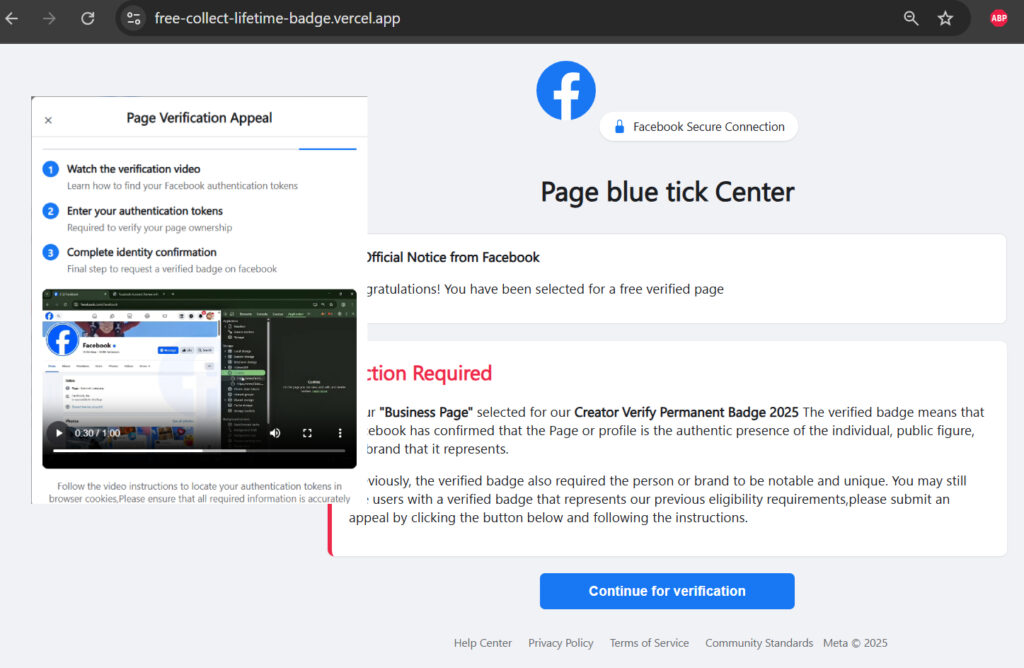
ClickFix has rapidly become one of the most common initial access techniques, accounting for 47 percent of observed attacks, according to Microsoft. The technique has evolved into multiple variants, including JackFix, CrashFix, and GlitchFix, each designed to exploit user trust through fake error messages and system prompts.
Recent campaigns have targeted social media creators by promising verified badges. Victims are instructed to copy browser authentication tokens into fake forms, leading to account takeover. Hunt.io estimates that such campaigns have used more than 115 web pages and multiple exfiltration endpoints since September 2025.

The rise of ClickFix builders, sold on underground forums for $200 to $1,500 per month, has further accelerated adoption. New platforms like ErrTraffic now specialize in ClickFix-style traffic distribution by deliberately breaking web pages and presenting fake fixes, a technique known as GlitchFix.
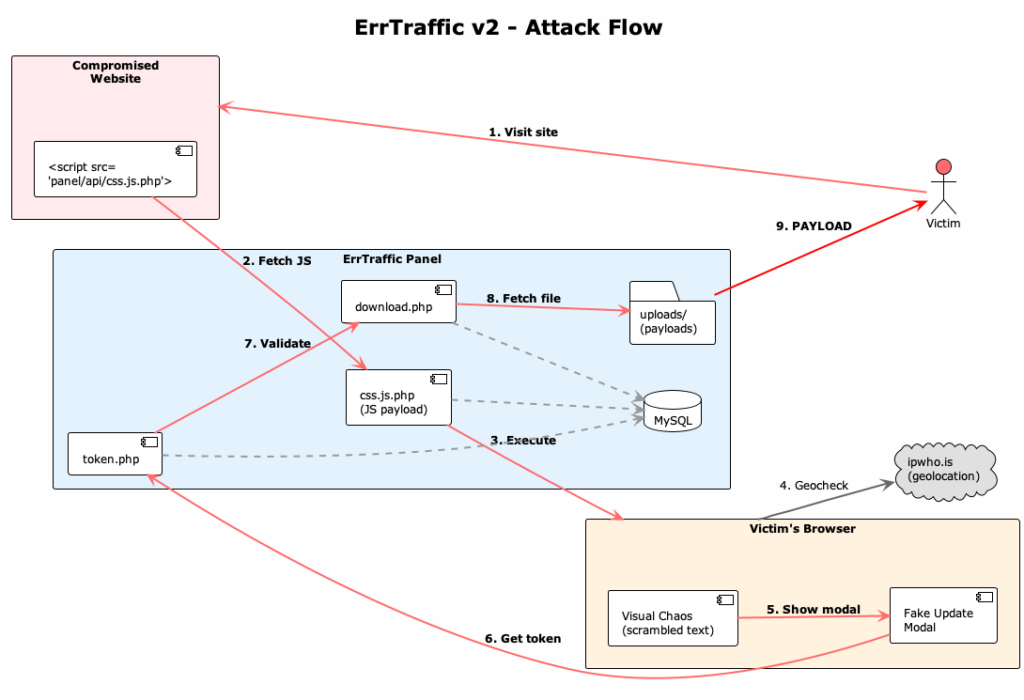
Researchers warn that defending against ClickFix attacks is especially difficult because the attack chains rely almost entirely on legitimate tools, trusted web services, and expected user behavior. As attackers continue to abuse default Windows components, cloud platforms, and content delivery networks, detection and prevention become increasingly challenging.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.