A clever blend of social engineering, stealthy delivery, and technical evasion has made ClickFix one of the fastest-growing malware tactics in recent cybersecurity history, according to a report by Guardio Labs.
“Just like a real-world virus variant, ClickFix quickly outpaced the infamous fake browser update scam,” said researcher Shaked Chen, sharing the findings with The Hacker News.
Unlike older scams that required users to download files, ClickFix removes that step. Instead, it tricks users into running a malicious command copied to their clipboard, making it both faster and harder to detect. The campaign has resulted in a rise in infections, from broad drive-by attacks to highly targeted phishing campaigns.
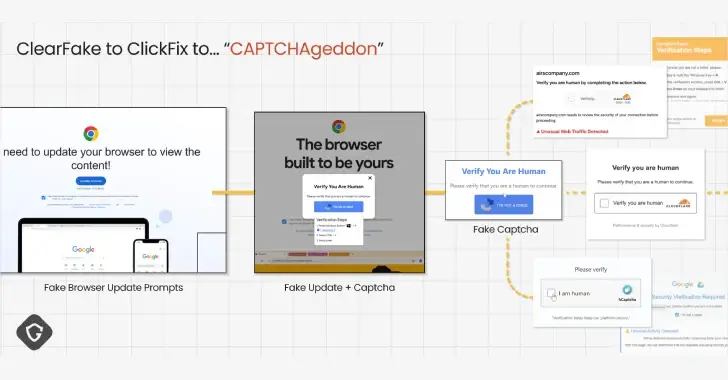
ClickFix was first observed in early 2024. It tricks users through deceptive CAPTCHA messages or fake error popups. These messages guide users to copy and paste a command—on Windows (Run dialog) or macOS (Terminal)—which starts a hidden malware chain.
The infection begins through vectors like:
- Phishing emails
- Drive-by downloads
- Malvertising
- SEO poisoning
Once the command is executed, it initiates a multi-stage sequence, downloading payloads that include info stealers, remote access trojans, and loaders.
The campaign has been so successful that researchers are calling it a CAPTCHAgeddon, with both criminal and nation-state actors using it in multiple attacks.
ClickFix is an evolved form of the earlier ClearFake scam. ClearFake used compromised WordPress sites to display fake browser update popups, which then delivered malware. Later versions of ClearFake even used Binance Smart Chain contracts (EtherHiding) to hide the malware.
Guardio notes that ClickFix succeeded by constantly improving its techniques. The attackers tested new types of messages, adding urgency or doubt to make users comply. They also used trusted infrastructure, like:
- Google Scripts to host fake CAPTCHA pages
- Legitimate-looking JavaScript files (e.g., socket.io.min.js) to hide payloads
- Obfuscation and dynamic loading to avoid detection
“This list of techniques—obfuscation, dynamic loading, cross-platform handling, third-party payload delivery—shows that threat actors are going beyond simple phishing tricks,” said Chen. “They are heavily investing in technical methods to keep their campaigns successful.”
ClickFix serves as a sharp reminder of how modern cyber threats continue to evolve. Users and defenders alike need to stay vigilant, keep systems updated, and never trust unexpected prompts or commands.