Cloudflare has once again proven the strength of its global defense infrastructure by automatically stopping a record-breaking 11.5 terabits per second (Tbps) distributed denial-of-service (DDoS) attack. This massive cyber offensive is now the largest volumetric DDoS attack ever mitigated, highlighting both the scale of modern threats and the growing sophistication of attackers.
The Attack in Numbers
According to Cloudflare, the attack peaked at 11.5 Tbps and 5.1 billion packets per second (Bpps). It was primarily a UDP flood sourced from Google Cloud infrastructure. Despite its staggering size, the attack was neutralized within 35 seconds, with no reported downtime.
Cloudflare noted on X (formerly Twitter):
“Over the past weeks, we have autonomously mitigated hundreds of hyper-volumetric DDoS attacks. The largest peaked at 11.5 Tbps.”
This rapid response shows how automated defenses are essential in countering the next generation of high-speed, short-lived cyberattacks.
Understanding Volumetric DDoS Attacks
Volumetric DDoS attacks are designed to overwhelm targets with a flood of traffic. This results in network congestion, packet loss, and eventual service disruption. Attackers often rely on botnets—compromised IoT devices, servers, or personal computers—that are infected with malware and controlled remotely.
Akamai explains the tactic further:
- The initial goal is to saturate bandwidth, disrupting internet and server connectivity.
- In some cases, volumetric attacks act as “smokescreens”, distracting defenders while other stealthier attacks are launched.
- These secondary attacks could involve data theft, financial fraud, or unauthorized account access.
Growing Wave of Hyper-Volumetric Attacks
This incident comes only months after Cloudflare stopped a 7.3 Tbps DDoS attack in May 2025. The company has reported an alarming surge in Layer 3/4 DDoS attacks exceeding 1 Tbps or 1 Bpps, which it refers to as hyper-volumetric attacks.
- Q1 2025: 700 attacks recorded
- Q2 2025: 6,500 attacks recorded
This exponential rise demonstrates how attackers are scaling their capabilities using compromised cloud environments and poorly secured IoT devices.
RapperBot and the IoT Botnet Threat
The Cloudflare 11.5 Tbps DDoS attack also coincides with discoveries around RapperBot, a botnet recently dismantled by law enforcement. RapperBot specifically targeted network video recorders (NVRs) and IoT devices, turning them into nodes for large-scale DDoS operations.
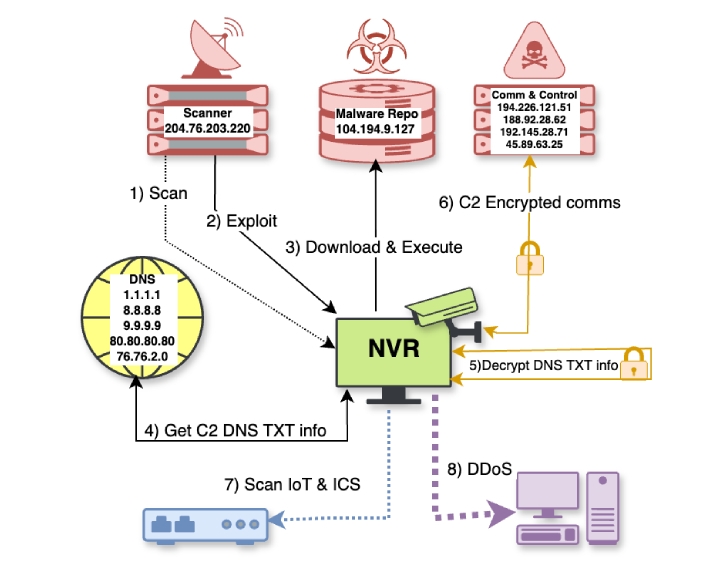
How RapperBot Works
- Exploits flaws in NVRs to steal administrator credentials.
- Uses a fake firmware update to push malicious code.
- Mounts a remote NFS file system to execute its payload.
- Fetches command-and-control (C2) server details through hard-coded DNS TXT records.
- Establishes an encrypted C2 connection to receive DDoS instructions.
- Continuously scans the internet for unpatched devices to expand its network.
Researchers highlight that persistence is not even required. Attackers simply keep scanning and reinfecting because so many devices remain exposed and vulnerable.
Why This Matters
The Cloudflare 11.5 Tbps DDoS Attack is more than just a record—it represents a dangerous escalation in how attackers leverage cloud platforms, automation, and IoT botnets. Cybercriminals are not only aiming to disrupt services but also to mask deeper, multi-vector intrusions.
Organizations must now:
- Harden their cloud environments.
- Regularly patch IoT and edge devices.
- Deploy automated DDoS mitigation systems.
- Monitor for secondary exploitation attempts during and after DDoS incidents.
Final Thoughts
Cloudflare’s quick response demonstrates the importance of automated cyber defense in an era where attacks are too fast and too massive for manual intervention. The record 11.5 Tbps DDoS attack should be seen as a wake-up call for businesses and governments alike—cybercriminals are scaling up, and only proactive, automated defense strategies can keep pace.


