The Russian advanced persistent threat (APT) group COLDRIVER has been linked to a new wave of ClickFix-style attacks, deploying two lightweight malware families identified as BAITSWITCH and SIMPLEFIX.
Researchers at Zscaler ThreatLabz detected the multi-stage ClickFix campaign earlier this month. They describe BAITSWITCH as a downloader that eventually drops SIMPLEFIX, a PowerShell-based backdoor.
COLDRIVER Expands Arsenal
Also tracked under aliases such as Callisto, Star Blizzard, and UNC4057, COLDRIVER has been active since 2019. The group is known for targeting diverse sectors, particularly through spear-phishing campaigns leading victims to credential-harvesting pages. Over time, it has introduced custom tools such as SPICA and LOSTKEYS, signaling its growing technical sophistication.
Google’s Threat Intelligence Group (GTIG) had previously documented COLDRIVER’s ClickFix tactics in May 2025. The campaign leveraged fake sites with bogus CAPTCHA prompts, tricking victims into running PowerShell commands that delivered the LOSTKEYS Visual Basic Script.
According to Zscaler researchers Sudeep Singh and Yin Hong Chang, the continued reliance on ClickFix shows that it remains an effective attack vector, even if it is not technically advanced.
Latest Campaign Techniques
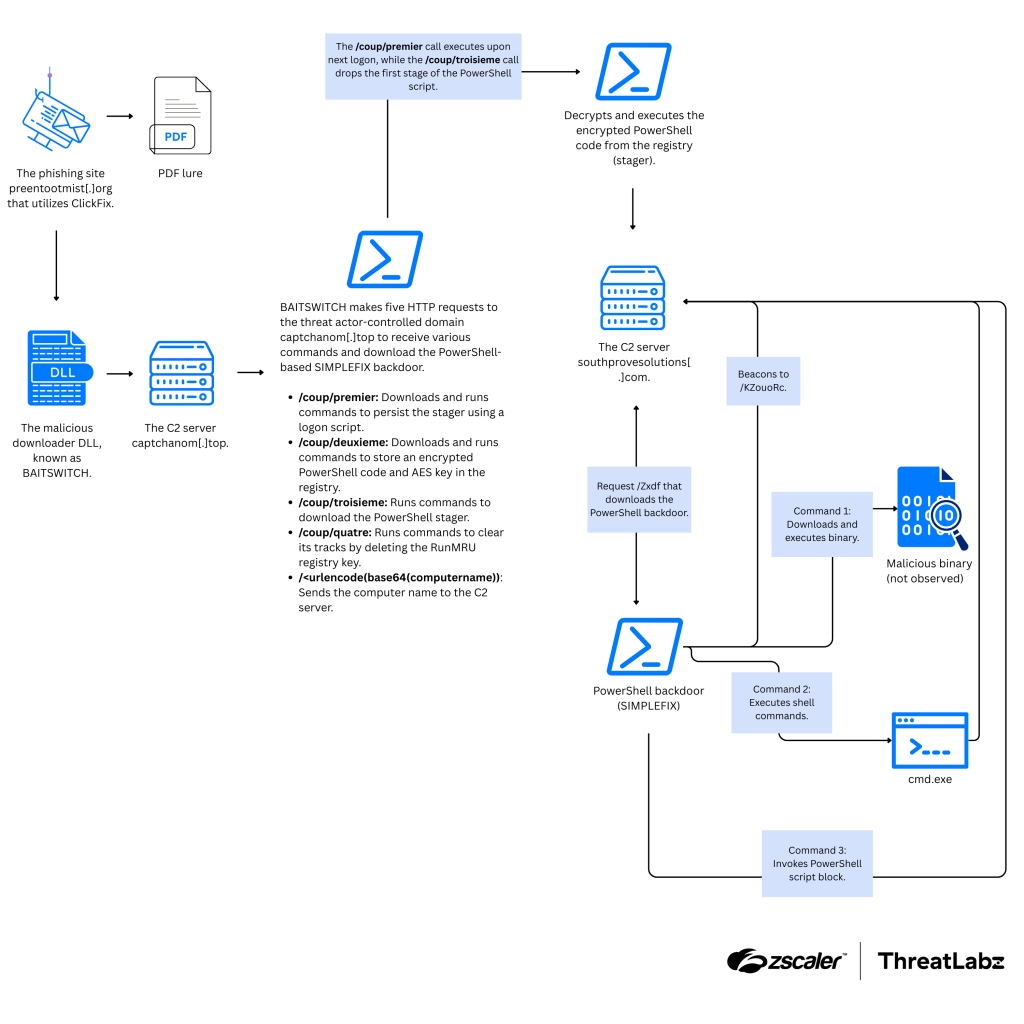
The most recent attacks follow a similar approach. Victims are tricked into executing a malicious DLL via the Windows Run dialog, disguised as a CAPTCHA verification step.
- The DLL (BAITSWITCH) connects to an attacker-controlled domain
captchanom[.]topto retrieve the SIMPLEFIX backdoor. - A decoy document hosted on Google Drive is presented to mislead victims.
- BAITSWITCH sends system details via HTTP requests, receives commands to establish persistence, and stores encrypted payloads in the Windows Registry.
- It also deploys a PowerShell stager and clears traces of executed commands to erase infection evidence.
The PowerShell stager then connects to southprovesolutions[.]com to download SIMPLEFIX, which communicates with a command-and-control (C2) server. Through this, attackers execute PowerShell scripts, commands, and binaries from remote sources.
One notable PowerShell script used by SIMPLEFIX exfiltrates files based on a predefined list of directories and extensions, sharing similarities with LOSTKEYS.
Zscaler further noted that COLDRIVER continues to target NGOs, human rights defenders, think tanks in Western regions, and individuals in exile from Russia, aligning with its consistent focus on civil society groups.
BO Team Phishing Attacks
Meanwhile, Kaspersky reported that the BO Team (also known as Black Owl, Hoody Hyena, and Lifting Zmiy) launched a phishing campaign in September 2025 against Russian companies.
The attack involved distributing password-protected RAR archives containing:
- An updated version of BrockenDoor rewritten in C#.
- A new iteration of ZeronetKit, a Golang backdoor.
ZeronetKit supports remote access, file operations, command execution, and tunneling. Advanced versions allow downloading and executing shellcode, updating communication intervals, and modifying C2 server lists. However, ZeronetKit lacks independent persistence, requiring BrockenDoor to place it in startup folders.
Rise of Bearlyfy
Another emerging group, Bearlyfy, has been leveraging ransomware strains like LockBit 3.0 and Babuk against Russian organizations. Initially, it demanded small ransoms from smaller firms but escalated to larger companies starting in April 2025.
By August 2025, Bearlyfy was estimated to have targeted at least 30 victims.
- In one case, the group exploited a vulnerable Bitrix version for initial access, later using the Zerologon flaw for privilege escalation.
- In another, access was obtained through a compromised partner company.
Ransom demands have ranged from a few thousand dollars to as high as €80,000 in cryptocurrency. Reports suggest that around 20% of victims have paid to recover their data.
Possible Links to PhantomCore
Analysis of Bearlyfy’s operations uncovered infrastructure overlaps with PhantomCore, a pro-Ukrainian group known for targeting Russian and Belarusian firms since 2022.
Despite these overlaps, researchers believe Bearlyfy operates as an independent entity, focusing on quick, impactful attacks. Unlike PhantomCore’s complex APT-style operations, Bearlyfy prefers minimal preparation, exploiting exposed services or vulnerable applications to rapidly encrypt or destroy data.


