Google’s Threat Intelligence Group (GTIG) has revealed new details about the Russian-linked hacking group known as COLDRIVER, uncovering three newly developed malware families that reflect the group’s increasing cyber activity since May 2025.
According to GTIG’s research, COLDRIVER has significantly expanded its malware arsenal just days after its previously known malware, LOSTKEYS, was publicly exposed. The quick adaptation suggests an accelerated operational pace from the threat group.
Although it remains unclear how long the development of these malware variants has been underway, Google confirmed that no new LOSTKEYS activity has been detected since its disclosure.
The newly identified malware families are named NOROBOT, YESROBOT, and MAYBEROBOT — collectively referred to as the “ROBOT” family. GTIG researcher Wesley Shields described them as “a collection of interconnected malware families linked through a unified delivery chain.”
Unlike COLDRIVER’s traditional approach, which typically focuses on stealing credentials from NGO officials, policy advisors, and dissidents, these latest attacks employ ClickFix-style social engineering lures. Victims are tricked into executing malicious PowerShell commands disguised as CAPTCHA verification prompts.
Earlier attack campaigns in January, March, and April 2025 led to the deployment of the information-stealing malware LOSTKEYS. However, later campaigns evolved into the ROBOT family. Independent cybersecurity researchers at Zscaler ThreatLabz have also tracked NOROBOT as BAITSWITCH and MAYBEROBOT as SIMPLEFIX.
Attack Chain Overview
The infection chain begins with an HTML-based ClickFix lure called COLDCOPY, which drops a DLL file (NOROBOT). This file is then executed using rundll32.exe, launching the next-stage payload.
Initial attack versions delivered a Python-based backdoor (YESROBOT), which was later replaced with a PowerShell implant (MAYBEROBOT).
YESROBOT communicates via HTTPS with a hard-coded command and control (C2) server, supporting file downloads, command execution, and document retrieval. Only two deployments of YESROBOT have been recorded, both occurring in late May 2025 soon after LOSTKEYS details were made public.
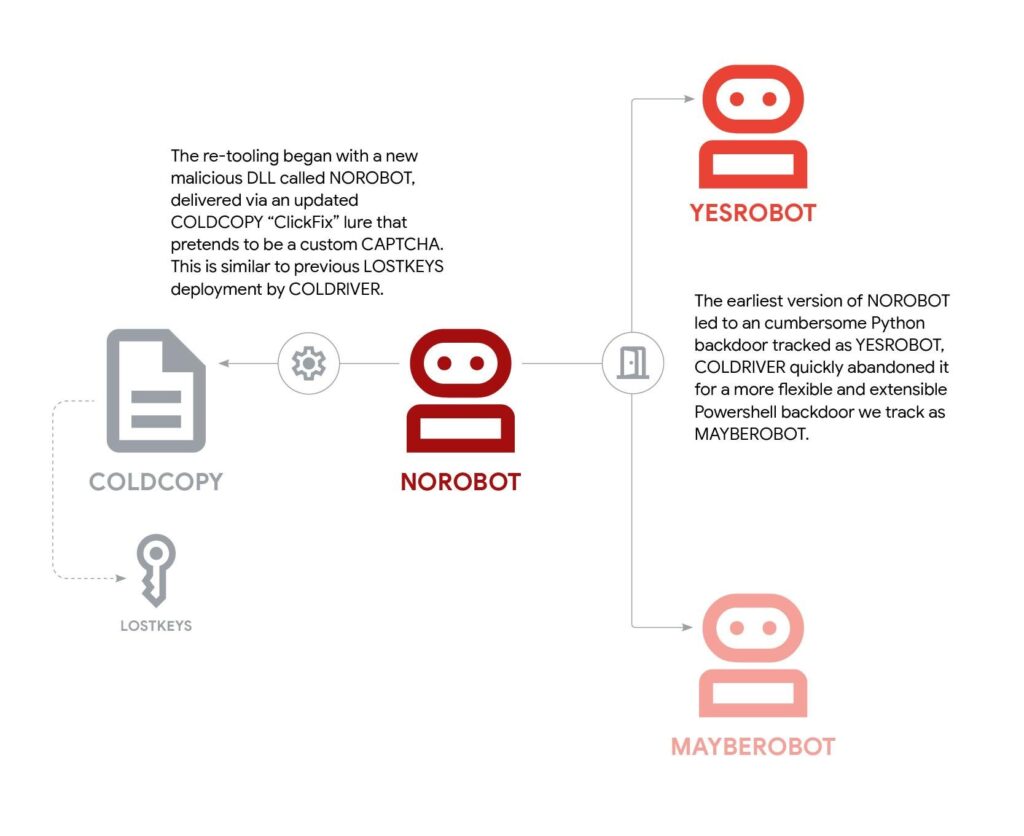
In comparison, MAYBEROBOT is more sophisticated and flexible. It can fetch and execute additional payloads from a remote URL, run Windows commands using cmd.exe, and execute PowerShell scripts.
Google analysts believe COLDRIVER may have used YESROBOT as a temporary fallback tool immediately after LOSTKEYS disclosure. This tool was soon replaced by MAYBEROBOT, as early NOROBOT versions suspiciously attempted to install Python 3.8 on compromised machines, making detection more likely.
According to GTIG, these malware families are primarily deployed against high-value targets who have already been compromised through phishing, allowing COLDRIVER to collect further intelligence.
Researcher Shields added, “NOROBOT and its associated infection chain have been under continuous evolution — initially simplified for successful deployment, and later made complex again by introducing split cryptographic keys.” This reflects COLDRIVER’s ongoing attempts to evade modern detection mechanisms.
Law Enforcement Developments
In a related case, the Netherlands’ Public Prosecution Service (Openbaar Ministerie, OM) announced that three 17-year-old suspects are under investigation for allegedly providing cyber services to a foreign government. One of them was reportedly in direct contact with a Russian government-affiliated hacker group.
OM stated, “The primary suspect instructed the others to map Wi-Fi networks across The Hague, and this information was shared with their client for payment. Such data can be exploited for digital espionage or cyberattacks.”
Two of the individuals were arrested on September 22, 2025, while the third, due to his limited involvement, remains under house arrest.
The Dutch authorities confirmed that there is no current evidence of coercion against the suspect communicating with the Russian-linked group.


