Commvault has issued critical security updates to patch four vulnerabilities that could allow attackers to execute remote code on vulnerable systems.
Affected Versions
The flaws exist in Commvault versions prior to 11.36.60. The vulnerabilities are:
- CVE-2025-57788 (CVSS 6.9): A flaw in the authentication process that lets unauthenticated attackers run API calls without valid credentials.
- CVE-2025-57789 (CVSS 5.3): A weakness during the setup phase that lets attackers exploit default credentials to gain administrator access before the first login.
- CVE-2025-57790 (CVSS 8.7): A severe path traversal issue enabling unauthorized file system access, which could lead to remote code execution.
- CVE-2025-57791 (CVSS 6.9): Insufficient input validation allows attackers to manipulate command-line arguments, escalating privileges within a low-privilege session.
Discovery and Fixes
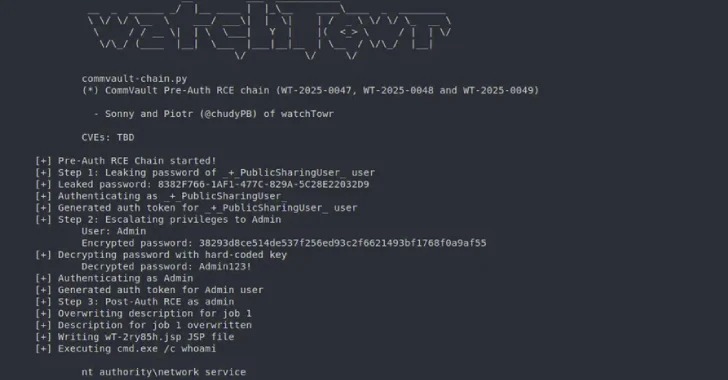
The vulnerabilities were discovered by Sonny Macdonald and Piotr Bazydlo from watchTowr Labs in April 2025. Commvault has since addressed these issues in versions 11.32.102 and 11.36.60. Notably, the Commvault SaaS platform remains unaffected.
Exploit Chains
Researchers noted that the flaws could be combined into two pre-authenticated exploit chains:
- Chain One: CVE-2025-57791 + CVE-2025-57790
- Chain Two: CVE-2025-57788 + CVE-2025-57789 + CVE-2025-57790
The second chain works only if the built-in admin password has not been changed after installation.
Background
This disclosure comes only months after watchTowr Labs reported another critical flaw in Commvault Command Center (CVE-2025-34028, CVSS 10.0), which allowed arbitrary code execution. Shortly after, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the bug to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
Key Takeaway
Organizations using Commvault should immediately update to 11.32.102 or 11.36.60 to protect their infrastructure from potential exploit chains.