A newly uncovered cyber offensive framework named Coruna, also tracked as CryptoWaters, has emerged as one of the most advanced iOS exploit kits observed in recent years. According to findings released by Google, the toolkit specifically targets Apple iPhone devices running iOS versions from 13.0 through 17.2.1. Devices operating on the latest iOS releases remain unaffected.
The investigation was conducted by the Google Threat Intelligence Group (GTIG), which described the framework as highly engineered and technically sophisticated. Initial details were first highlighted by WIRED.
Advanced Multi Chain iOS Exploitation Framework
Researchers confirmed that Coruna includes five complete iOS exploit chains containing a total of 23 vulnerabilities. Several of these exploits rely on non public techniques and mitigation bypass strategies rarely seen outside high level surveillance operations.
According to Google Threat Intelligence Group (GTIG), the strength of this exploit kit lies in its structured integration. Each exploit component is interconnected through shared utility and exploitation frameworks, forming a seamless attack pipeline. This level of engineering suggests professional development typically associated with state grade spyware capabilities.
Evolution From Surveillance Tool To Criminal Weapon
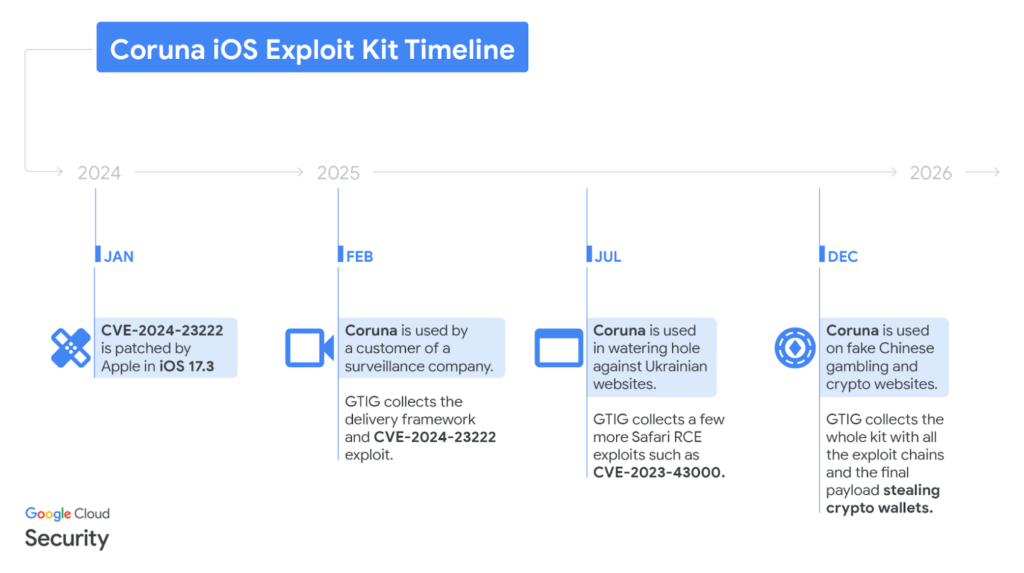
Threat intelligence analysis indicates that the exploit kit has changed hands multiple times since February 2025. It reportedly began within a commercial surveillance vendor environment, later transitioned to a government backed threat actor, and by December ended up with a financially motivated attacker operating from China.
The transfer pathway remains unclear. However, the case highlights a growing underground marketplace for second hand zero day exploits. Once exclusive surveillance grade capabilities are increasingly being repurposed by nation state actors and eventually cybercriminal groups.
Mobile security firm iVerify noted structural similarities between Coruna and earlier frameworks linked to actors affiliated with the United States government. Researchers described it as a critical example of advanced spyware proliferation from private surveillance companies into state actors and ultimately criminal ecosystems.
First Signs Of Mass iOS Exploitation
Security experts believe this campaign marks the first known instance of wide scale exploitation targeting iOS devices rather than highly selective attacks. Historically, iOS spyware operations were precision targeted. Coruna signals a shift toward broader deployment models.
Google first detected portions of an exploit chain early last year. The malicious code was embedded inside a previously unseen JavaScript framework. The framework fingerprints visiting devices to confirm authenticity and extract system details such as device model and exact iOS version.
After profiling the device, the framework dynamically loads an appropriate WebKit remote code execution exploit and executes a pointer authentication code bypass. One of the key vulnerabilities involved was CVE-2024-23222, a WebKit type confusion flaw patched by Apple in January 2024 through iOS 17.3 and iPadOS 17.3, as well as iOS 16.7.5 and iPadOS 16.7.5.
Targeted Campaigns In Ukraine And China
In July 2025, the same JavaScript exploitation framework appeared on the domain cdn.uacounter[.]com. It was injected as a hidden iFrame within compromised Ukrainian websites, including industrial equipment portals, retail platforms, service providers, and ecommerce sites. The activity is attributed to a suspected Russian espionage cluster tracked as UNC6353.
Notably, the malicious payload was selectively delivered only to specific iPhone users within certain geographic regions. The deployed exploits included CVE-2024-23222, CVE-2022-48503, and CVE-2023-43000, the latter being a WebKit use after free vulnerability originally patched in iOS 16.6 and iPadOS 16.6 in July 2023. Apple later updated the release documentation in November 2025 to formally list the vulnerability.
By December 2025, the framework resurfaced again. This time it was distributed through a network of fraudulent Chinese finance related websites. Visitors were instructed to access the sites using an iPhone or iPad for an optimized experience. Once accessed, a hidden iFrame delivered the Coruna exploit kit without geographic restrictions. This campaign is associated with threat cluster UNC6691.
Breakdown Of Exploited Vulnerabilities
Further forensic investigation uncovered a debug build of the exploit kit along with complete exploit chains covering multiple iOS generations. The toolkit targets vulnerabilities across iOS 13 to iOS 17.2.1.
Key exploited components include:
• Neutron – CVE-2020-27932 targeting iOS 13.x
• Dynamo – CVE-2020-27950 targeting iOS 13.x
• buffout – CVE-2021-30952, affecting iOS 13 through 15.1.1
• jacurutu – CVE-2022-48503, targeting iOS 15.2 through 15.5
• IronLoader – CVE-2023-32409 targeting iOS 16.0 through 16.4.0
• Photon – CVE-2023-32434 targeting iOS 14.5 through 15.7.6
• Gallium – CVE-2023-38606 affecting iOS 14.x
• Parallax – CVE-2023-41974 targeting iOS 16.4 through 16.7
• terrorbird – CVE-2023-43000 targeting iOS 16.2 through 16.5.1
• cassowary – CVE-2024-23222 targeting iOS 16.6 through 17.2.1
• Sparrow – CVE-2024-23225 targeting iOS 17.0 through 17.3
• Rocket – CVE-2024-23296 targeting iOS 17.1 through 17.4
Researchers noted that Photon and Gallium previously appeared as zero day exploits during Operation Triangulation. Coruna incorporates reusable exploitation modules to streamline vulnerability chaining.
Malware Payload And Data Theft Capabilities
Threat cluster UNC6691 leveraged the exploit kit to deploy a loader known as PlasmaLoader, also referred to as PLASMAGRID. This stager binary decodes QR codes embedded in images and retrieves additional modules from remote servers.
The malware focuses heavily on cryptocurrency theft and data exfiltration. Targeted applications include Base, Bitget Wallet, Exodus, and MetaMask. The implant contains hard coded command and control servers, along with a fallback mechanism utilizing a custom domain generation algorithm seeded with the term lazarus. Generated domains use the .xyz top level domain and are validated through Google public DNS resolution.
Defensive Evasion And Security Recommendations
A notable defensive evasion feature is that Coruna avoids execution on devices running Lockdown Mode or when users browse in private mode. This indicates awareness of Apple security features and an effort to reduce detection.
Security experts strongly recommend keeping iOS devices fully updated to the latest available version. Enabling Lockdown Mode provides an additional layer of protection against advanced spyware threats and zero day exploitation attempts.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.