Cybersecurity researchers have uncovered an active malware campaign that abuses cracked software websites and popular video platforms to distribute advanced loader malware, primarily CountLoader and GachiLoader. The activity highlights how threat actors continue to exploit user trust in free software and online tutorials to silently compromise systems.
Researchers from Cyderes revealed that cracked software distribution sites are being leveraged to spread an updated version of CountLoader, a modular and stealth focused malware loader. According to the Cyderes Howler Cell Threat Intelligence team, CountLoader acts as the first stage in a multi step intrusion chain designed to gain initial access, evade defenses, and deploy additional malicious payloads.
CountLoader is not a new threat. It has previously been analyzed by Fortinet and Silent Push, both of which documented its ability to deploy secondary malware such as Cobalt Strike, AdaptixC2, PureHVNC RAT, Amatera Stealer, and cryptomining tools. Evidence suggests the loader has been active in the wild since at least June 2025.
The latest infection chain begins when victims attempt to download pirated versions of legitimate applications, including Microsoft Word. Instead of receiving the expected software, users are redirected to a MediaFire link hosting a malicious ZIP archive. This archive contains an encrypted ZIP file and a decoy Microsoft Word document that provides the password needed to extract the second archive.
Inside the extracted content is a renamed but legitimate Python interpreter labeled as Setup.exe. This binary is configured to execute a malicious command that retrieves CountLoader version 3.2 from a remote server using mshta.exe, allowing the malware to blend into normal system activity.
To maintain persistence, CountLoader creates a scheduled task disguised as a Google component, using a name such as GoogleTaskSystem136.0.7023.12 combined with an identifier like string. The task is set to run every 30 minutes for a period of up to 10 years, repeatedly launching mshta.exe and contacting a fallback command and control domain.
The malware also performs security checks by querying Windows Management Instrumentation to determine whether CrowdStrike Falcon is installed. If Falcon is detected, the persistence command is modified to execute through cmd.exe before launching mshta.exe, a tactic designed to bypass endpoint defenses.
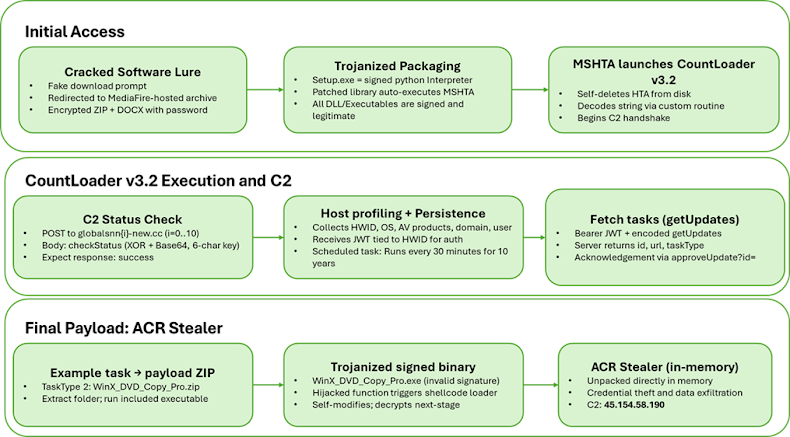
Beyond persistence, CountLoader profiles infected systems and retrieves additional payloads. The newest iteration introduces the ability to propagate through removable USB drives and execute malicious code directly in memory using mshta.exe or PowerShell. Its capabilities include downloading and executing executables, DLLs, MSI installers, and ZIP based modules, removing scheduled tasks, exfiltrating detailed system data, spreading via malicious shortcut files, and running remote PowerShell payloads entirely in memory.
In the campaign analyzed by Cyderes, the final payload delivered by CountLoader was ACR Stealer, an information stealing malware designed to harvest sensitive data from compromised hosts. Researchers emphasized that the attack demonstrates an increasing reliance on signed binaries and fileless execution techniques to evade detection.
YouTube Ghost Network Delivers GachiLoader
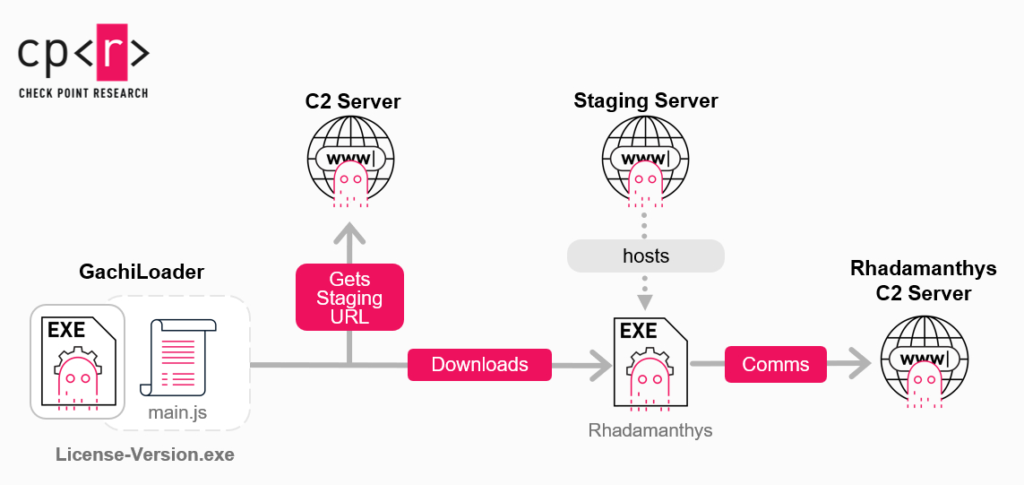
In a related disclosure, Check Point reported on a separate but equally concerning malware campaign involving a JavaScript based loader known as GachiLoader. Written in Node.js, the malware is distributed through what researchers describe as the YouTube Ghost Network, a collection of compromised YouTube accounts used to push malicious content.
One observed variant of GachiLoader deploys a secondary malware called Kidkadi, which introduces a novel approach to Portable Executable injection. According to Check Point researchers Sven Rath and Jaromír Hořejší, the technique involves loading a legitimate DLL and abusing Vectored Exception Handling to replace it dynamically with a malicious payload.
Investigators identified nearly 100 YouTube videos associated with the campaign, collectively reaching around 220,000 views. These videos were uploaded from 39 hijacked accounts, with the earliest traced back to December 22, 2024. Most of the malicious videos have since been removed by Google.
In some cases, GachiLoader has been used to deploy the Rhadamanthys information stealer. Like other modern loaders, it focuses on delivering follow on payloads while performing extensive anti analysis checks. The malware attempts to determine whether it is running with elevated privileges by executing the net session command. If unsuccessful, it relaunches itself with administrator rights, triggering a User Account Control prompt that unsuspecting users may approve.

During the final stage of execution, GachiLoader attempts to disable security defenses by terminating SecHealthUI.exe, a process linked to Microsoft Defender. It then configures Defender exclusions for common directories such as C:\Users, C:\ProgramData, and C:\Windows, reducing the likelihood of detection. The loader either fetches the final payload directly or uses an additional component named kidkadi.node to complete the infection via Vectored Exception Handling abuse.
Check Point concluded that the operators behind GachiLoader demonstrate a strong understanding of Windows internals and are actively evolving known techniques to evade modern defenses. The campaign underscores the growing risk posed by fake installers, cracked software, and compromised social media platforms as malware distribution channels.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


