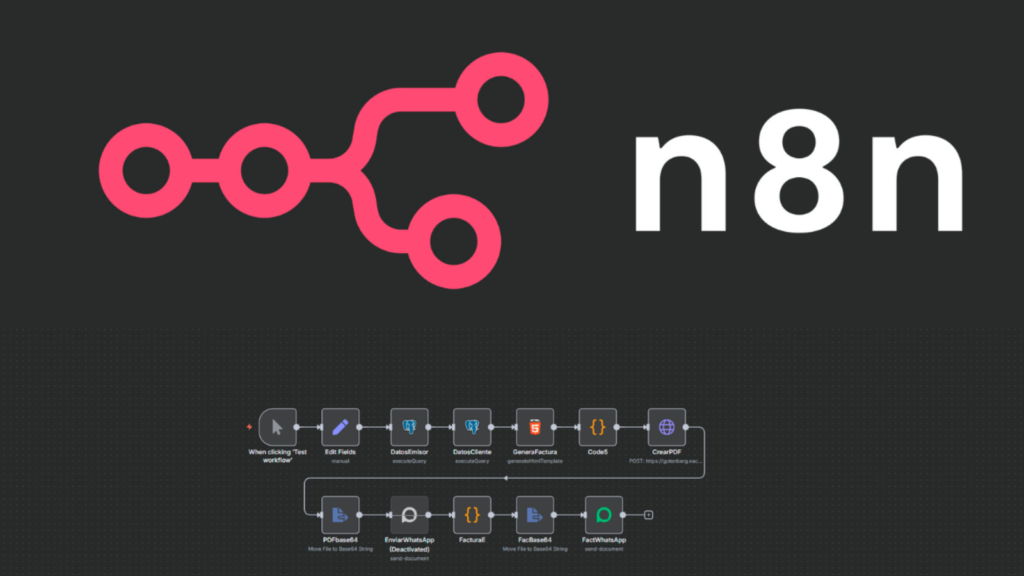
Cybersecurity researchers have revealed a highly severe security flaw in the n8n workflow automation platform that could allow attackers to execute arbitrary code on vulnerable systems under specific conditions.
The vulnerability is tracked as CVE-2025-68613 and has received a CVSS score of 9.9, placing it among the most critical software flaws disclosed this year. The issue was identified and responsibly reported by security researcher Fatih Çelik. According to npm statistics, the n8n package currently records around 57,000 weekly downloads, highlighting the scale of potential exposure.
According to the maintainers of the npm package, the weakness arises when expressions provided by authenticated users during workflow configuration are evaluated in an execution environment that lacks proper isolation from the underlying runtime. This behavior opens the door for abuse by authenticated attackers.
If successfully exploited, the flaw allows an attacker to execute arbitrary code with the same privileges as the n8n process. This could lead to complete system compromise, including unauthorized access to sensitive data, manipulation of workflows, and execution of system level commands.
The vulnerability impacts all versions starting from 0.211.0 up to but not including 1.120.4. The issue has been addressed in versions 1.120.4, 1.121.1, and 1.122.0, and users are strongly encouraged to upgrade immediately.
According to attack surface management platform Censys, there are approximately 103,476 potentially exposed n8n instances as of December 22, 2025. The highest concentration of vulnerable deployments has been observed in the United States, Germany, France, Brazil, and Singapore.

Given the critical nature of the vulnerability, users who cannot apply patches immediately are advised to restrict workflow creation and editing permissions to trusted users only. Additionally, deploying n8n in a hardened environment with limited operating system privileges and restricted network access can significantly reduce the risk of exploitation.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.