Cybersecurity researchers have revealed details about multiple serious vulnerabilities in the n8n workflow automation platform, including two critical flaws that could allow attackers to execute arbitrary commands on affected systems.
The vulnerabilities have already been patched, but security experts warn that systems running older versions may remain vulnerable.
Key Vulnerabilities Identified
Researchers identified two major security issues that could potentially allow remote code execution.
- CVE-2026-27577 (CVSS 9.4), Expression sandbox escape leading to remote code execution
- CVE-2026-27493 (CVSS 9.5), Unauthenticated expression evaluation through n8n Form nodes
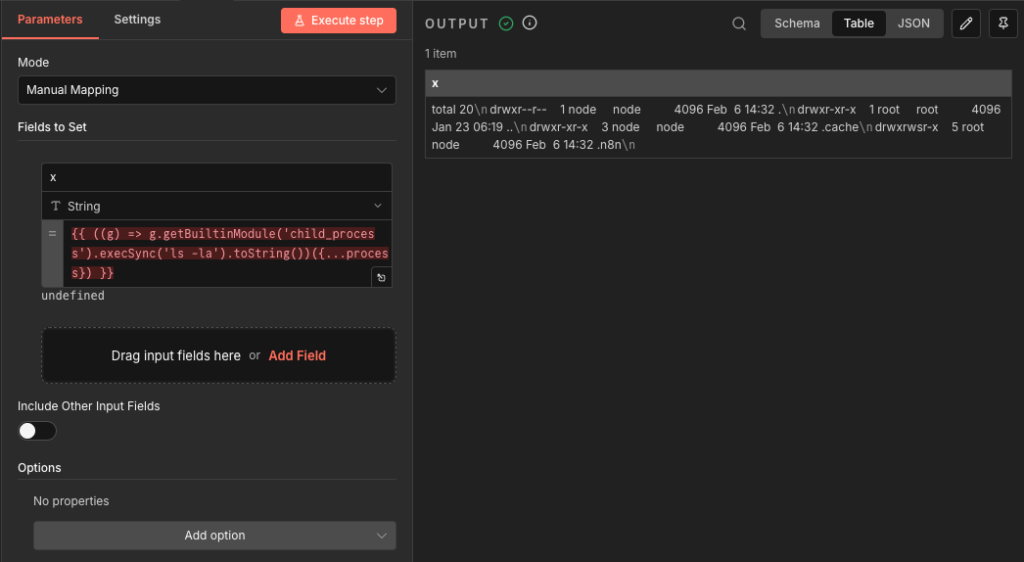
According to Pillar Security researcher Eilon Cohen, who discovered and reported the vulnerabilities, CVE-2026-27577 is caused by a flaw in the expression compiler. A missing transformation case in the Abstract Syntax Tree (AST) rewriter allows the system process object to bypass restrictions, enabling full remote code execution for authenticated expressions.
Exploitation Through Public Forms
The second vulnerability, CVE-2026-27493, originates from what researchers describe as a double evaluation bug in the Form nodes of n8n.
Since form endpoints are publicly accessible by design and do not require authentication, attackers could inject malicious expressions. In a typical scenario, a malicious actor could exploit a public “Contact Us” form by inserting a specially crafted payload into the Name field, triggering execution of shell commands on the server.
Chaining Vulnerabilities for Full System Compromise
Security researchers warn that when CVE-2026-27493 is combined with the sandbox escape vulnerability CVE-2026-27577, attackers could achieve full remote code execution on the n8n host system.
These vulnerabilities affect both self-hosted and cloud deployments of n8n in the following versions:
- Versions below 1.123.22
- Versions 2.0.0 to 2.9.2
- Versions 2.10.0
The issues have been fixed in:
- 1.123.22
- 2.9.3
- 2.10.1
Temporary Mitigation Measures
If immediate patching is not possible, n8n recommends several temporary security measures.
For CVE-2026-27577:
- Restrict workflow creation and editing permissions to trusted users only
- Deploy n8n in a hardened environment with limited operating system privileges and restricted network access
For CVE-2026-27493:
- Manually review all Form node usage
- Disable Form nodes using the environment variable
NODES_EXCLUDE=n8n-nodes-base.form - Disable Form Trigger nodes using
NODES_EXCLUDE=n8n-nodes-base.formTrigger
However, maintainers emphasize that these steps only reduce risk temporarily and do not fully resolve the vulnerabilities.
Risk of Credential Theft
Researchers also warn that attackers could potentially access the N8N_ENCRYPTION_KEY environment variable, which protects sensitive credentials stored in the platform.
If obtained, this key could allow attackers to decrypt critical information including:
- AWS access keys
- Database credentials
- OAuth tokens
- API keys
Additional Critical Vulnerabilities Patched
The latest security updates also address two additional critical flaws that could allow arbitrary code execution.
- CVE-2026-27495 (CVSS 9.4)
Code injection vulnerability in the JavaScript Task Runner sandbox that allows execution outside the sandbox environment. - CVE-2026-27497 (CVSS 9.4)
A vulnerability in the Merge node’s SQL query mode that could allow attackers to execute code and create arbitrary files on the server.
To reduce risk:
- For CVE-2026-27495, administrators should enable external runner mode using
N8N_RUNNERS_MODE=external - For CVE-2026-27497, the Merge node can be disabled using
NODES_EXCLUDE=n8n-nodes-base.merge
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


