CrossC2 Expands Cobalt Strike Capabilities to Linux and macOS
A new advanced cyber campaign has surfaced, leveraging CrossC2, an unofficial extension of Cobalt Strike, to extend its functionality from Windows systems into Linux and macOS environments.
Multi-Stage Attack Chain
Between September and December 2024, researchers observed a series of incidents involving this cross-platform malware, signaling a major shift from the traditional Windows-centered attacks. The campaign relies on a multi-layered infection chain, beginning with legitimate processes and gradually loading more harmful components.
Attackers combined PsExec, Plink, standard Cobalt Strike modules, and the new CrossC2 extension, building a versatile framework that could breach Active Directory infrastructures across different operating systems.
Evidence shows the campaign was not limited to Japan, as submissions on VirusTotal suggest activity in several other countries as well.
Custom Loader: ReadNimeLoader
Analysts at JPCert identified a new malware loader named ReadNimeLoader, specifically crafted to deploy Cobalt Strike payloads.
This loader, developed in the Nim programming language, integrates anti-analysis features that set it apart from conventional malware delivery methods.
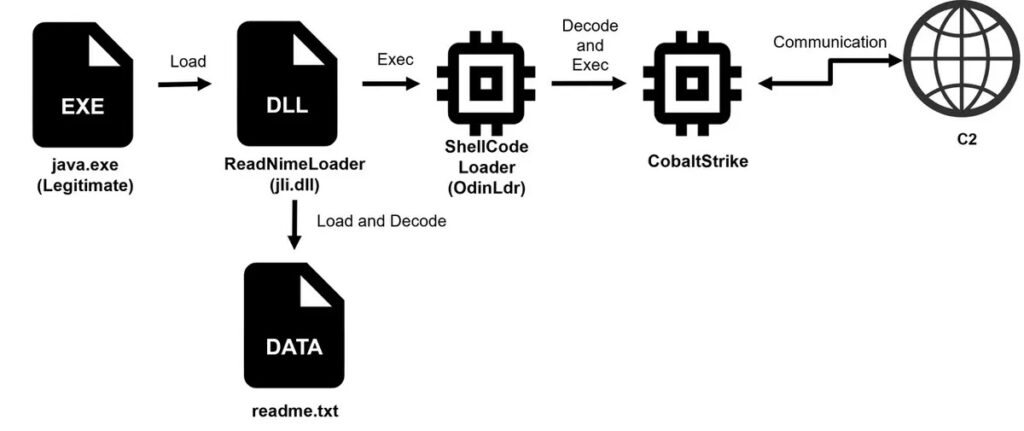
The infection chain often begins with java.exe launched via scheduled tasks, which then performs DLL sideloading to execute malicious DLL files.
Advanced Anti-Analysis Techniques
ReadNimeLoader incorporates four unique anti-debugging methods designed to frustrate malware analysts:
- Checking the BeingDebugged flag within the Process Environment Block (PEB)
- Verifying CONTEXT_DEBUG_REGISTER values
- Detecting time discrepancies using elapsed time calculations
- Using exception-based debugging detection
A standout feature is the key generation method. Portions of the decryption key are embedded directly within the anti-analysis functions, making it impossible to retrieve the correct key without executing these protections.
The payload decryption process uses AES-256-ECB encryption, with keys derived through advanced string decoding functions. The malware also integrates two XOR-based decoding methods, and later updates added an additional decode02 function, reflecting continuous development by the threat actors.
Expanding Threat Landscape
This evolution highlights a concerning security trend. Cross-platform malware expansion means that attackers can now compromise systems traditionally considered less at risk. Since many Linux servers lack strong endpoint detection and response (EDR) solutions, adversaries gain longer dwell time and greater opportunity for lateral movement across networks.