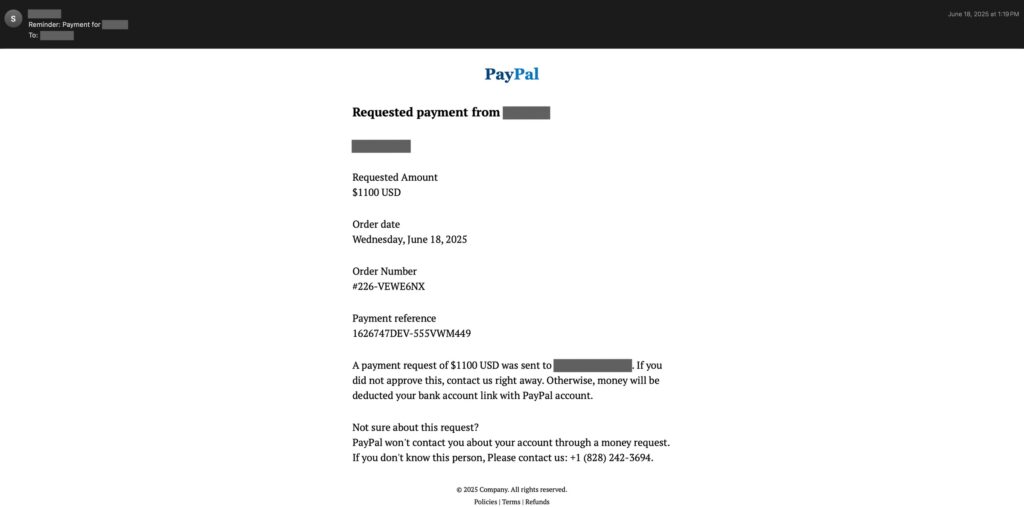
A rising email evasion technique, called hidden-text salting, is becoming a serious problem for email security, enabling attackers to hide large amounts of irrelevant or misleading content inside otherwise malicious messages. By abusing CSS properties and HTML structure, adversaries keep this content invisible to human recipients while confusing automated detection engines, including signature-based systems and AI-driven classifiers.
How the attack works
Hidden-text salting embeds extra content, or salt, into different parts of an email, then uses presentation-layer tricks so the text does not display to users. Common injection points include preheaders, headers, message bodies, and HTML attachments. Each location offers unique benefits for evasion, for example, preheader injection alters preview text shown by email clients, while header manipulation can break language or metadata analysis.
Body injection is the most common approach, because it allows threat actors to dilute malicious signals with large volumes of hidden text. Attachment-based salting, in contrast, hides content inside HTML files or documents attached to messages, complicating static analysis performed by security products.
Why it bypasses detection
This technique undermines both traditional and modern defenses. Signature engines rely on exact string matches, which salt can break, while machine learning models that analyze visible text can be misled when hidden content is mixed with visible content. Researchers observed that even small amounts of concealed text can change sentiment analysis or intent classification enough to flip a message from malicious to benign in an algorithmic assessment.
Cisco Talos identified this pattern after monitoring email campaigns from March 2024 through July 2025, finding that hidden-text salting appears far more often in malicious mail than in legitimate communications. Various threat actors, from opportunistic spammers to advanced persistent threat groups, are using simple insertions, multilingual salt, and complex obfuscation to defeat detection.
Technical implementation methods
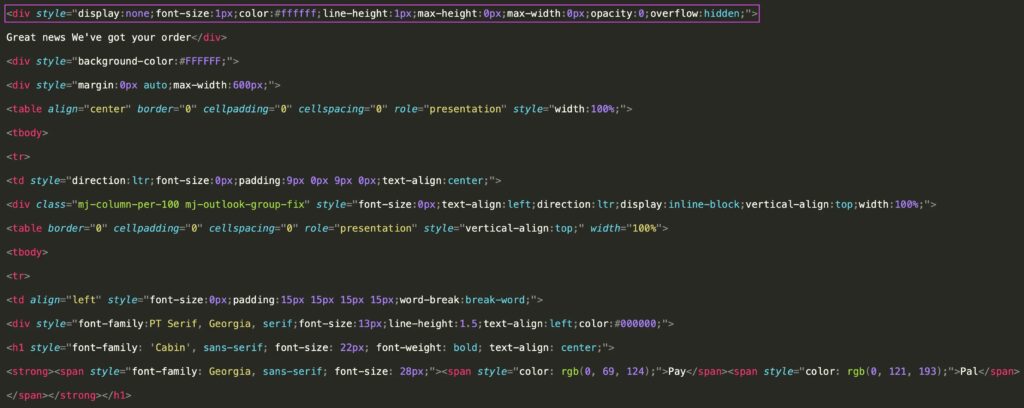
Attackers use three broad categories of CSS and HTML techniques for concealment, often combining them for robustness.
- Text properties, for example setting font-size to zero, matching font color to the background, or manipulating line-height so characters collapse, prevent content from being rendered while leaving it in the HTML source.
- Visibility controls, such as display:none, visibility:hidden, or opacity:0, remove elements from visual rendering but keep them accessible in the DOM for parsers that do not consider styling.
- Dimensional constraints, where containers are given zero height or width, max-height:0, max-width:0, and overflow:hidden, clip oversized content so it is not visible on-screen yet remains in the HTML.
Advanced variants add conditional styling, using media queries or client-specific selectors to ensure hidden content stays concealed across desktop email clients, mobile apps, and webmail. Some campaigns apply CSS selectors broadly to multiple elements, reducing code repetition while ensuring consistent hiding behavior.
Character-level injection is another tactic, inserting zero-width space or zero-width non-joiner characters between letters of sensitive strings. These invisible characters break exact-string matching used by signature-based filters, without affecting human readability.
Example snippet used by adversaries:
<div style="font-size: 0px, color: #ffffff, line-height: 1px, max-height: 0px, max-width: 0px, opacity: 0, overflow: hidden;">
Hidden salt content here
</div>Detection challenges and implications
Hidden-text salting is effective against parsers that extract only visible text, and it can also fool models that do not account for styling context. As organizations add large language models and other AI tools to their defensive stacks, the risk grows that hidden content will manipulate automated classification, allowing malicious messages to bypass filters and reach inboxes.
Because the technique is relatively easy to implement and hard to detect without style-aware parsing, it has spread across phishing, spam, and targeted espionage campaigns. The diversity of implementations, from single-property concealment to multi-layered, responsive designs, increases the burden on security vendors and enterprise defenders.
Recommendations and conclusion
Defenders should adopt multi-layered analysis that includes style-aware HTML parsing, detection of zero-width characters, and heuristics that flag unusually large volumes of non-visible text. Email security tools need to normalize rendered content, evaluate both the DOM and computed styles, and use structural checks to identify suspicious elements, for example, containers with many characters but zero rendered area.
In summary, hidden-text salting marks an evolution in email evasion tactics, leveraging CSS and HTML to hide content from users while exploiting weaknesses in automated analysis. To reduce the impact, security teams must expand detection beyond plain text extraction, incorporate styling context into analysis pipelines, and monitor for the variety of concealment patterns observed in recent threat intelligence.