A newly uncovered phishing operation called the ZipLine campaign is actively targeting U.S. manufacturing companies. The attackers disguise themselves as business partners and exploit supply chain importance to deliver a fileless, memory-resident malware known as MixShell.
Unconventional Phishing Tactics
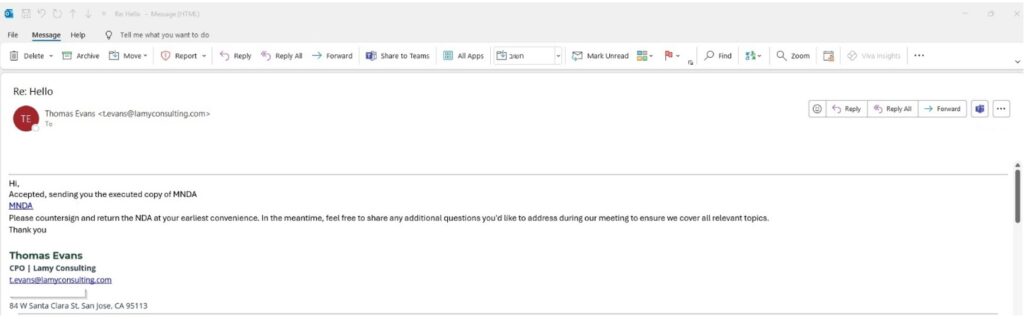
Unlike traditional phishing methods, ZipLine reverses the workflow. Instead of sending the first email, threat actors initiate contact through corporate “Contact Us” forms. Once a response is received, they maintain an ongoing exchange of emails—sometimes for two weeks—before sending a malicious ZIP archive hosted on a trusted Platform-as-a-Service (PaaS) domain.
Malicious Archive and Payload Execution
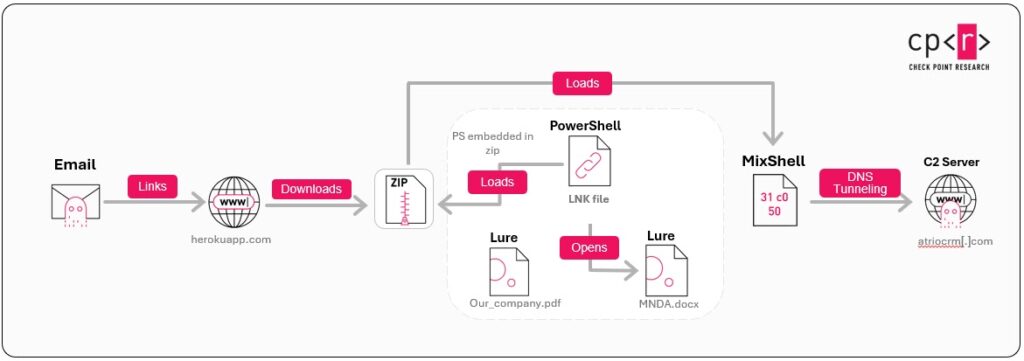
The ZIP file includes a .lnk shortcut and an embedded PowerShell script, hidden alongside harmless PDF and DOCX decoy files. When executed, the .lnk file loads the archive, extracts a PowerShell script marked with delimiters, and injects it directly into memory. This process bypasses AMSI by forcing AmsiUtils.amsiInitFailed = $true, ensuring security tools cannot easily detect it.
Memory-Only Malware Behavior
Picus Security researchers report that MixShell’s design avoids writing files to disk, making it highly evasive. Using System.Reflection.Emit and a custom ROR4 hashing algorithm, the malware dynamically loads Windows API functions while unwrapping its shellcode entirely in memory.
The implant’s configuration is stored in an XOR-encrypted, hex-encoded block, which provides DNS TXT tunneling details for command-and-control (C2) communication. If DNS fails after six attempts, MixShell switches to HTTP fallback, blending malicious requests with normal web traffic.
Persistence Through COM Hijacking
To survive reboots, MixShell hijacks a COM object by altering the TypeLib registry entry. It creates a malicious XML scriptlet (Udate_Srv.sct) inside the ProgramData folder and associates it with the Internet Explorer Web Browser CLSID. This ensures the payload automatically restarts whenever Explorer.exe triggers the hijacked COM component.
Infection Flow in Detail
The attack chain showcases both social engineering and technical stealth. Attackers lure victims by submitting form-based inquiries, often under the guise of an “AI Impact Assessment.” They then request a signed NDA, delivering a ZIP file via a Herokuapp subdomain.

Inside the archive, the PowerShell script extracts the shellcode blob marked with xFIQCV, then uses Windows functions like VirtualAlloc to load and run it directly in memory. By dynamically resolving functions at runtime, MixShell avoids detection from signature-based defenses.
A Serious Challenge for Defenders
Because MixShell executes entirely in memory, it leaves behind almost no artifacts, significantly complicating forensic investigations. Organizations in the manufacturing sector—especially those tied to supply chains—must remain alert to this stealthy threat and adopt stronger detection strategies for fileless malware.